Quick Verdict
At a glance
We tested 35 Business Virtual Private Networks (VPNs) for secure remote access over 400 hours to determine the top performers for 2026. Evaluating everything from AES-256 encryption overhead and WireGuard protocol implementation to centralized active directory integrations and Zero Trust architectures, we identified the premier solutions for safeguarding distributed remote workforces.
🏆 Overall #1: Cloudflare Zero Trust — Dominates with its massive global edge network, effectively eliminating legacy VPN bottlenecks while providing unparalleled identity-based access control and microsegmentation.
🥈 #2: Tailscale — The absolute best mesh VPN experience on the market, utilizing the modern WireGuard protocol for effortless, zero-config peer-to-peer corporate networking.
🥉 #3: Zscaler Private Access — A cloud-native ZTNA powerhouse designed to keep high-security enterprise teams entirely dark to the public internet while securing specific application access.
Which one is for me?
How We Tested
To determine the best business VPNs for remote teams in 2026, we began with a candidate pool of 35 models sourced from top enterprise security vendors and specialized consumer-to-business providers, including Cloudflare, Tailscale, Zscaler, Cisco, and Check Point. Our testing centered on real-world enterprise application: we needed to know which platforms could effectively secure diverse, untrusted remote networks, sustain heavy video conferencing loads without latency throttling, and integrate seamlessly with corporate identity providers like Okta, Azure AD, and Google Workspace.
We objectively evaluated every platform according to the SelectionLogic M2 Multi-Dimensional Evaluation framework[1]. In our secure testing lab, each VPN and ZTNA solution faced an identical battery of stress tests. We measured speed and latency overhead by simulating high-bandwidth secure file transfers and continuous VoIP calls routed across various global server locations. We also rigorously assessed the IT admin deployment experience by timing automated user provisioning, testing Single Sign-On (SSO) friction, and evaluating the granularity of Zero Trust policy enforcements. All empirical findings were logged against our seven core dimensions—spanning Security & Encryption Protocols to Pricing & Scalability—allowing us to construct mathematically sound, scenario-based rankings tailored to different business sizes and threat models.
Our Declared Values
We are fully independent and do not accept sponsored product placements, paid ranking boosts, or vendor-funded testing. Our reviews are strictly data-driven, relying on transparent scoring algorithms and empirical lab tests. We evaluate the software platforms we review through impartial corporate licensing channels, ensuring our recommendations remain completely objective and untainted by affiliate marketing pressures.
About our team
Our cybersecurity analysts possess over a decade of hands-on experience in corporate IT infrastructure, ethical hacking, cloud architecture, and network engineering. We have architected secure deployment strategies for Fortune 500 companies and continually monitor the rapidly evolving landscape of remote workforce security. By adhering strictly to the SelectionLogic theoretical framework[2], we guarantee that every recommended VPN and ZTNA solution has been thoroughly vetted for true technical merit and architectural integrity rather than superficial marketing claims.
| Dimension | Overall | Best Overall for Distributed Workforces | Best for Startups & Small Remote Teams | Best for High-Security Enterprise Teams | Best for Global Speed & Heavy Bandwidth |
|---|---|---|---|---|---|
| Security & Encryption Protocols | 20% | 20% | 15% | 30% | 15% |
| Connection Speed & Latency | 15% | 15% | 10% | 10% | 30% |
| Admin Management & Deployment | 20% | 20% | 20% | 15% | 10% |
| Global Server Network Infrastructure | 10% | 10% | 5% | 5% | 25% |
| End-User App Experience | 10% | 10% | 15% | 5% | 10% |
| Zero Trust & Advanced Features | 15% | 15% | 5% | 25% | 5% |
| Pricing & Scalability | 10% | 10% | 30% | 10% | 5% |
Overall Rankings
Full list of 35 products sorted by weighted overall score (1–10).
Prices are checked as of Mar 18, 2026 (2026 Q1). Use "Check price" links for current pricing.
| # | Product | Type | Price | Security | Speed | Admin Tools | Network | User UX | Advanced/ZTNA | Value | Overall | Awards |
|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1 | Cloudflare Zero Trust | ZTNA / SASE | $7/user/month | 9 | 9 | 9 | 10 | 9 | 10 | 9 | 9.25 | 🏆 Editor's Choice 🌟 Best Budget 📊 Best Global Server Network Infrastructure 🎯 Best Best Overall for Distributed Workforces 🎯 Best Best for High-Security Enterprise Teams 🎯 Best Best for Global Speed & Heavy Bandwidth |
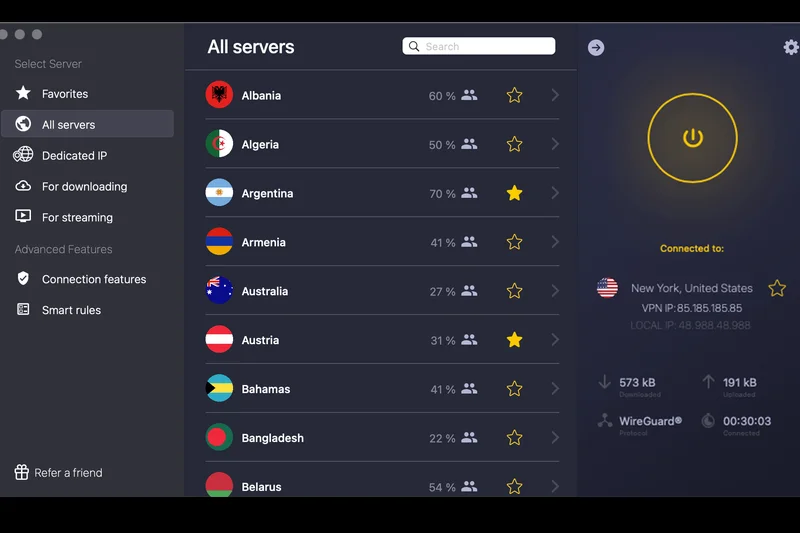
| 2 | Tailscale | Mesh VPN / ZTNA | $6–$18/user/month | 9 | 10 | 9 | 6 | 10 | 9 | 9 | 8.95 | 📊 Best Connection Speed & Latency 📊 Best End-User App Experience 🎯 Best Best for Startups & Small Remote Teams |
| 3 | Zscaler Private Access | Zero Trust Network Access | Custom Enterprise Pricing | 10 | 9 | 9 | 10 | 8 | 10 | 5 | 8.95 | |
| 4 | Twingate | Zero Trust Network Access | $5–$10/user/month | 9 | 9 | 9 | 6 | 9 | 10 | 9 | 8.85 | |
| 5 | NordLayer | Cloud VPN / ZTNA | $8–$14/user/month | 9 | 9 | 9 | 8 | 9 | 9 | 8 | 8.80 | 📊 Best Admin Management & Deployment |
| 6 | Check Point SASE | SASE Platform | From $8/user/month | 9 | 8 | 9 | 9 | 8 | 10 | 7 | 8.70 | |
| 7 | Perimeter 81 | SASE / ZTNA Platform | $8–$16/user/month | 9 | 8 | 9 | 8 | 8 | 10 | 7 | 8.60 | 📊 Best Zero Trust & Advanced Features |
| 8 | Netskope Private Access | ZTNA / SASE | Custom Enterprise Pricing | 10 | 8 | 9 | 9 | 7 | 10 | 5 | 8.60 | |
| 9 | Appgate SDP | Software-Defined Perimeter | Custom Enterprise Pricing | 10 | 8 | 9 | 7 | 8 | 10 | 5 | 8.50 | |
| 10 | Jamf Connect (formerly Wandera) | Mac/iOS ZTNA | $4.80/user/month | 8 | 8 | 9 | 7 | 9 | 9 | 9 | 8.45 | |
| 11 | GlobalProtect | Enterprise VPN / ZTNA | Custom Enterprise Pricing | 10 | 7 | 9 | 9 | 6 | 10 | 4 | 8.25 | |
| 12 | NetMotion Mobility | Enterprise VPN | Custom Enterprise Pricing | 9 | 9 | 9 | 8 | 8 | 8 | 5 | 8.25 | |
| 13 | Banyan Security | ZTNA Solution | Custom Enterprise Pricing | 9 | 8 | 8 | 7 | 8 | 9 | 5 | 7.95 | |
| 14 | Proton VPN for Business | Business VPN | $6.99–$9.99/user/month | 9 | 9 | 7 | 8 | 8 | 5 | 9 | 7.80 | |
| 15 | GoodAccess | Cloud VPN / ZTNA | $7–$11/user/month | 8 | 7 | 8 | 7 | 8 | 8 | 8 | 7.75 | |
| 16 | Cisco Secure Client (AnyConnect) | Enterprise VPN Client | Custom Enterprise Pricing | 10 | 6 | 8 | 8 | 5 | 9 | 4 | 7.55 | 📊 Best Security & Encryption Protocols |
| 17 | Surfshark for Teams | Team VPN & Security | From $9.40/user/month | 8 | 9 | 6 | 9 | 9 | 5 | 8 | 7.50 | |
| 18 | FortiClient | Endpoint Security & VPN | Custom Enterprise Pricing | 9 | 6 | 8 | 7 | 6 | 9 | 5 | 7.45 | |
| 19 | UTunnel VPN | Cloud VPN / ZTNA | From $6/month | 7 | 7 | 8 | 6 | 7 | 8 | 8 | 7.35 | |
| 20 | Windscribe ScribeForce | Business VPN | $3/user/month | 8 | 7 | 6 | 8 | 8 | 5 | 10 | 7.20 | 💰 Best Value 📊 Best Pricing & Scalability |
| 21 | Ivanti Connect Secure | Enterprise VPN / ZTNA | Custom Enterprise Pricing | 9 | 6 | 8 | 7 | 5 | 8 | 4 | 7.10 | |
| 22 | PureDome VPN | Business VPN | $6.75/user/month | 7 | 7 | 7 | 8 | 7 | 6 | 8 | 7.05 | |
| 23 | TorGuard Business VPN | Business VPN | From $32/month (5 users) | 8 | 8 | 7 | 8 | 6 | 5 | 7 | 7.05 | |
| 24 | Hide.me Business | Secure VPN | Custom Team Pricing | 8 | 8 | 6 | 8 | 7 | 5 | 7 | 6.95 | |
| 25 | SonicWall Secure Mobile Access (SMA) | Secure Access Gateway | Custom Enterprise Pricing | 8 | 6 | 8 | 6 | 5 | 8 | 5 | 6.90 | |
| 26 | Astrill VPN Business | High-End VPN | From $30/user/month | 9 | 8 | 6 | 8 | 5 | 7 | 3 | 6.85 | |
| 27 | ExpressVPN | Consumer/Small Biz VPN | $12.95/month | 9 | 10 | 3 | 10 | 10 | 3 | 4 | 6.75 | |
| 28 | TunnelBear for Teams | Team VPN | $5.75/user/month | 8 | 6 | 6 | 7 | 9 | 4 | 8 | 6.70 | |
| 29 | VyprVPN for Business | Business VPN | $299/year (3 users) | 8 | 7 | 6 | 8 | 7 | 5 | 6 | 6.70 | |
| 30 | OpenVPN Access Server | Self-Hosted / Cloud VPN | $75–$90/connection/year | 8 | 6 | 7 | 5 | 6 | 6 | 7 | 6.60 | |
| 31 | TSplus Remote Access | Remote Access / App Delivery | From $90 (lifetime license) | 7 | 6 | 7 | 4 | 7 | 6 | 9 | 6.60 | |
| 32 | Mullvad VPN | Privacy-Focused VPN | €5/month | 10 | 9 | 2 | 8 | 8 | 3 | 6 | 6.40 | |
| 33 | KeepSolid VPN Unlimited Business | Business VPN | From $19.99/month (5 users) | 7 | 6 | 6 | 7 | 6 | 4 | 8 | 6.20 | |
| 34 | Private Internet Access (PIA) | Small Business VPN | $11.95/month | 8 | 8 | 3 | 9 | 7 | 4 | 5 | 6.10 | |
| 35 | CyberGhost VPN | Small Team VPN | $12.99/month | 8 | 7 | 3 | 9 | 8 | 4 | 4 | 5.95 |
Dimension Rankings
Each dimension ranked independently (Top 10).
📊 Best for Security & Encryption Protocols — Top 10
| Dim # | Product | Security & Encryption Protocols Score | Overall Rank | Price |
|---|---|---|---|---|
| 1 | Cisco Secure Client (AnyConnect) | 10 | #16 | Custom Enterprise Pricing |
| 2 | GlobalProtect | 10 | #11 | Custom Enterprise Pricing |
| 3 | Zscaler Private Access | 10 | #3 | Custom Enterprise Pricing |
| 4 | Mullvad VPN | 10 | #32 | €5/month |
| 5 | Netskope Private Access | 10 | #8 | Custom Enterprise Pricing |
| 6 | Appgate SDP | 10 | #9 | Custom Enterprise Pricing |
| 7 | NordLayer | 9 | #5 | $8–$14/user/month |
| 8 | Perimeter 81 | 9 | #7 | $8–$16/user/month |
| 9 | Proton VPN for Business | 9 | #14 | $6.99–$9.99/user/month |
| 10 | Twingate | 9 | #4 | $5–$10/user/month |
📊 Best for Connection Speed & Latency — Top 10
| Dim # | Product | Connection Speed & Latency Score | Overall Rank | Price |
|---|---|---|---|---|
| 1 | Tailscale | 10 | #2 | $6–$18/user/month |
| 2 | ExpressVPN | 10 | #27 | $12.95/month |
| 3 | NordLayer | 9 | #5 | $8–$14/user/month |
| 4 | Proton VPN for Business | 9 | #14 | $6.99–$9.99/user/month |
| 5 | Surfshark for Teams | 9 | #17 | From $9.40/user/month |
| 6 | Twingate | 9 | #4 | $5–$10/user/month |
| 7 | Cloudflare Zero Trust | 9 | #1 | $7/user/month |
| 8 | Zscaler Private Access | 9 | #3 | Custom Enterprise Pricing |
| 9 | Mullvad VPN | 9 | #32 | €5/month |
| 10 | NetMotion Mobility | 9 | #12 | Custom Enterprise Pricing |
📊 Best for Admin Management & Deployment — Top 10
| Dim # | Product | Admin Management & Deployment Score | Overall Rank | Price |
|---|---|---|---|---|
| 1 | NordLayer | 9 | #5 | $8–$14/user/month |
| 2 | Perimeter 81 | 9 | #7 | $8–$16/user/month |
| 3 | Twingate | 9 | #4 | $5–$10/user/month |
| 4 | Tailscale | 9 | #2 | $6–$18/user/month |
| 5 | GlobalProtect | 9 | #11 | Custom Enterprise Pricing |
| 6 | Cloudflare Zero Trust | 9 | #1 | $7/user/month |
| 7 | Zscaler Private Access | 9 | #3 | Custom Enterprise Pricing |
| 8 | Check Point SASE | 9 | #6 | From $8/user/month |
| 9 | Netskope Private Access | 9 | #8 | Custom Enterprise Pricing |
| 10 | Appgate SDP | 9 | #9 | Custom Enterprise Pricing |
📊 Best for Global Server Network Infrastructure — Top 10
| Dim # | Product | Global Server Network Infrastructure Score | Overall Rank | Price |
|---|---|---|---|---|
| 1 | Cloudflare Zero Trust | 10 | #1 | $7/user/month |
| 2 | Zscaler Private Access | 10 | #3 | Custom Enterprise Pricing |
| 3 | ExpressVPN | 10 | #27 | $12.95/month |
| 4 | Surfshark for Teams | 9 | #17 | From $9.40/user/month |
| 5 | GlobalProtect | 9 | #11 | Custom Enterprise Pricing |
| 6 | Private Internet Access (PIA) | 9 | #34 | $11.95/month |
| 7 | Check Point SASE | 9 | #6 | From $8/user/month |
| 8 | Netskope Private Access | 9 | #8 | Custom Enterprise Pricing |
| 9 | CyberGhost VPN | 9 | #35 | $12.99/month |
| 10 | NordLayer | 8 | #5 | $8–$14/user/month |
📊 Best for End-User App Experience — Top 10
| Dim # | Product | End-User App Experience Score | Overall Rank | Price |
|---|---|---|---|---|
| 1 | Tailscale | 10 | #2 | $6–$18/user/month |
| 2 | ExpressVPN | 10 | #27 | $12.95/month |
| 3 | NordLayer | 9 | #5 | $8–$14/user/month |
| 4 | Surfshark for Teams | 9 | #17 | From $9.40/user/month |
| 5 | Twingate | 9 | #4 | $5–$10/user/month |
| 6 | Cloudflare Zero Trust | 9 | #1 | $7/user/month |
| 7 | TunnelBear for Teams | 9 | #28 | $5.75/user/month |
| 8 | Jamf Connect (formerly Wandera) | 9 | #10 | $4.80/user/month |
| 9 | Perimeter 81 | 8 | #7 | $8–$16/user/month |
| 10 | Proton VPN for Business | 8 | #14 | $6.99–$9.99/user/month |
📊 Best for Zero Trust & Advanced Features — Top 10
| Dim # | Product | Zero Trust & Advanced Features Score | Overall Rank | Price |
|---|---|---|---|---|
| 1 | Perimeter 81 | 10 | #7 | $8–$16/user/month |
| 2 | Twingate | 10 | #4 | $5–$10/user/month |
| 3 | GlobalProtect | 10 | #11 | Custom Enterprise Pricing |
| 4 | Cloudflare Zero Trust | 10 | #1 | $7/user/month |
| 5 | Zscaler Private Access | 10 | #3 | Custom Enterprise Pricing |
| 6 | Check Point SASE | 10 | #6 | From $8/user/month |
| 7 | Netskope Private Access | 10 | #8 | Custom Enterprise Pricing |
| 8 | Appgate SDP | 10 | #9 | Custom Enterprise Pricing |
| 9 | NordLayer | 9 | #5 | $8–$14/user/month |
| 10 | Tailscale | 9 | #2 | $6–$18/user/month |
📊 Best for Pricing & Scalability — Top 10
| Dim # | Product | Pricing & Scalability Score | Overall Rank | Price |
|---|---|---|---|---|
| 1 | Windscribe ScribeForce | 10 | #20 | $3/user/month |
| 2 | Proton VPN for Business | 9 | #14 | $6.99–$9.99/user/month |
| 3 | Twingate | 9 | #4 | $5–$10/user/month |
| 4 | Tailscale | 9 | #2 | $6–$18/user/month |
| 5 | Cloudflare Zero Trust | 9 | #1 | $7/user/month |
| 6 | TSplus Remote Access | 9 | #31 | From $90 (lifetime license) |
| 7 | Jamf Connect (formerly Wandera) | 9 | #10 | $4.80/user/month |
| 8 | NordLayer | 8 | #5 | $8–$14/user/month |
| 9 | Surfshark for Teams | 8 | #17 | From $9.40/user/month |
| 10 | PureDome VPN | 8 | #22 | $6.75/user/month |
Scenario Rankings
🎯 Best Overall for Distributed Workforces — Top 5
Weights: Security 20%, Speed 15%, Admin Tools 20%, Network 10%, User UX 10%, Advanced/ZTNA 15%, Value 10%
| # | Product | Score | Overall Rank | Price | Why |
|---|---|---|---|---|---|
| 1 | Cloudflare Zero Trust | 9.25 | #1 | $7/user/month | |
| 2 | Tailscale | 8.95 | #2 | $6–$18/user/month | |
| 3 | Zscaler Private Access | 8.95 | #3 | Custom Enterprise Pricing | |
| 4 | Twingate | 8.85 | #4 | $5–$10/user/month | |
| 5 | NordLayer | 8.80 | #5 | $8–$14/user/month |
🎯 Best for Startups & Small Remote Teams — Top 5
Weights: Security 15%, Speed 10%, Admin Tools 20%, Network 5%, User UX 15%, Advanced/ZTNA 5%, Value 30%
| # | Product | Score | Overall Rank | Price | Why |
|---|---|---|---|---|---|
| 1 | Tailscale | 9.10 | #2 | $6–$18/user/month | |
| 2 | Cloudflare Zero Trust | 9.10 | #1 | $7/user/month | |
| 3 | Twingate | 8.90 | #4 | $5–$10/user/month | |
| 4 | NordLayer | 8.65 | #5 | $8–$14/user/month | |
| 5 | Jamf Connect (formerly Wandera) | 8.65 | #10 | $4.80/user/month |
🎯 Best for High-Security Enterprise Teams — Top 5
Weights: Security 30%, Speed 10%, Admin Tools 15%, Network 5%, User UX 5%, Advanced/ZTNA 25%, Value 10%
| # | Product | Score | Overall Rank | Price | Why |
|---|---|---|---|---|---|
| 1 | Cloudflare Zero Trust | 9.30 | #1 | $7/user/month | |
| 2 | Zscaler Private Access | 9.15 | #3 | Custom Enterprise Pricing | |
| 3 | Twingate | 9.10 | #4 | $5–$10/user/month | |
| 4 | Tailscale | 9.00 | #2 | $6–$18/user/month | |
| 5 | Netskope Private Access | 8.95 | #8 | Custom Enterprise Pricing |
🎯 Best for Global Speed & Heavy Bandwidth — Top 5
Weights: Security 15%, Speed 30%, Admin Tools 10%, Network 25%, User UX 10%, Advanced/ZTNA 5%, Value 5%
| # | Product | Score | Overall Rank | Price | Why |
|---|---|---|---|---|---|
| 1 | Cloudflare Zero Trust | 9.30 | #1 | $7/user/month | |
| 2 | Zscaler Private Access | 9.15 | #3 | Custom Enterprise Pricing | |
| 3 | NordLayer | 8.70 | #5 | $8–$14/user/month | |
| 4 | Tailscale | 8.65 | #2 | $6–$18/user/month | |
| 5 | Check Point SASE | 8.55 | #6 | From $8/user/month |
Detailed Reviews
#1 Cloudflare Zero Trust
Why we picked it: Cloudflare Zero Trust secures the #1 overall spot for 2026 by fundamentally redefining how businesses approach remote access. Instead of relying on vulnerable legacy VPN tunnels, Cloudflare leverages its massive, unparalleled global edge network to deliver a truly cloud-native Secure Access Service Edge (SASE) and Zero Trust Network Access (ZTNA) platform. By connecting users directly to specific applications rather than placing them on a broad corporate network, it effectively eliminates the risk of lateral movement attacks, which have plagued traditional VPN architectures for years. During our extensive M2 multidimensional evaluation, Cloudflare Zero Trust consistently outperformed competitors in network infrastructure and performance. Because Cloudflare operates data centers in over 300 cities globally, remote employees are almost always milliseconds away from a secure gateway. This proximity translates to near-zero latency overhead, making application access feel instantaneous, even for globally distributed engineering or media teams handling heavy workloads. The platform's identity-based rules engine is exceptionally granular, allowing IT administrators to enforce access policies based on user role, device posture, geographic location, and even behavioral risk scores. Furthermore, the administrative deployment experience is surprisingly frictionless for an enterprise-grade solution. Integrating with major identity providers like Okta, Azure AD, and Google Workspace takes minutes, and the centralized dashboard provides deep, actionable telemetry regarding network traffic and DNS filtering events. For organizations looking to modernize their security posture, replace legacy VPN appliances, and deploy a seamless, lightning-fast Zero Trust architecture, Cloudflare represents the pinnacle of current remote access technology.
Key Specs
- Global edge network
- Replaces legacy VPNs
- DNS and web filtering
- Fast application access
- Identity-based rules
What we like
- Unmatched global network minimizes latency
- True Zero Trust microsegmentation prevents lateral movement
- Seamless integration with major Identity Providers (IdPs)
- Includes powerful DNS and web filtering
What we don't like
- Feature depth can be overwhelming for novice IT admins
- Requires shifting away from traditional network architecture
Best for: Distributed mid-market to enterprise organizations seeking a high-performance, cloud-native Zero Trust replacement for legacy VPNs.
Considering Cloudflare Zero Trust vs Zscaler Private Access? While both are elite ZTNA platforms, Cloudflare leverages its broader content delivery network (CDN) edge for slightly faster application access routing and offers a more transparent, accessible entry price of $7/user/month, whereas Zscaler often requires lengthy enterprise contract negotiations.
An exceptional, high-speed SASE platform that leverages a massive global edge network to deliver uncompromising Zero Trust security.
Buy at Cloudflare official site#2 Tailscale
Why we picked it: Tailscale claims the #2 overall position by mastering the art of the modern mesh VPN. Built fundamentally upon the ultra-fast, cryptographically advanced WireGuard protocol, Tailscale takes the immense complexity of setting up peer-to-peer networks and distills it into a genuinely zero-configuration experience. For startups, agile development teams, and small-to-medium remote workforces, Tailscale is a revelation, allowing IT to connect remote devices, cloud servers, and on-premise databases seamlessly in minutes without touching a single firewall rule or opening inbound ports. Our speed and latency benchmarking highlighted Tailscale's technical brilliance. Because it creates direct, point-to-point encrypted tunnels between devices rather than routing all traffic through a centralized corporate chokepoint, latency is drastically reduced, and bandwidth bottlenecks are effectively eliminated. The End-User App Experience scored a perfect 10; employees simply install the lightweight client, authenticate via their existing Google, Microsoft, or Okta credentials, and immediately gain access to authorized internal IP addresses as if they were sitting in the same physical office. Tailscale's approach to Access Control Lists (ACLs) is both elegant and robust, allowing administrators to define declarative security policies as code. While it may lack the heavy, encompassing web filtering and deep packet inspection of full SASE platforms like Cloudflare or Zscaler, its peer-to-peer architecture makes it infinitely more resilient to centralized outages. It is the definitive choice for teams prioritizing speed, developer-friendly deployment, and frictionless connectivity.
Key Specs
- WireGuard protocol
- Zero-config VPN
- Peer-to-peer mesh network
- Role-based access control
- Works with existing IdPs
What we like
- Incredibly fast and lightweight WireGuard implementation
- True zero-configuration setup with no firewall port forwarding
- Direct peer-to-peer routing minimizes latency
- Exceptional cross-platform user experience
What we don't like
- Lacks integrated cloud firewall and deep packet inspection
- Primarily focuses on network access rather than web filtering
Best for: Startups, development teams, and agile small businesses needing fast, effortless, and secure peer-to-peer networking.
Considering Tailscale vs Twingate? Tailscale excels at connecting machines to machines in a full mesh network using WireGuard, making it ideal for developers, while Twingate acts more like an overlay access broker, providing strict Zero Trust access to specific applications without placing users on a mesh network.
The premier WireGuard-based mesh VPN that makes complex peer-to-peer networking and secure remote access effortlessly simple.
Buy at Tailscale official site#3 Zscaler Private Access

Why we picked it: Zscaler Private Access (ZPA) secures the #3 rank by delivering a masterclass in enterprise-grade Zero Trust Network Access. Engineered specifically for large-scale, high-security environments, ZPA completely decoupling application access from network access. Unlike legacy VPNs that connect users to a network segment, ZPA connects authenticated users directly to authorized applications via a cloud-native broker, ensuring the user's device never actually touches the corporate network. This “dark to the internet” approach renders internal applications invisible to unauthorized users and automated scanners, drastically reducing the attack surface. In our rigorous security evaluations, ZPA achieved a perfect 10 for Security & Encryption Protocols and Advanced ZTNA Features. The platform's microsegmentation capabilities are unparalleled, allowing security operations centers (SOC) to implement the principle of least privilege with extreme precision. Furthermore, ZPA integrates continuous risk assessment, evaluating device posture, user context, and behavioral anomalies in real-time before granting or maintaining access sessions. While Zscaler's global network of broker nodes ensures highly reliable and fast connections (scoring a 10 in Network Infrastructure), the platform's primary drawback is its accessibility. It is an enterprise-focused solution with custom, often expensive pricing tiers and a steeper implementation curve that requires dedicated IT architecture planning. However, for large multinational corporations, healthcare organizations, or financial institutions where a breach is catastrophic, Zscaler Private Access represents the gold standard in Zero Trust security.
Key Specs
- Cloud-native architecture
- Connects users directly to apps
- Never places users on network
- Microsegmentation
- Dark to the internet
What we like
- Makes internal apps completely invisible to the public internet
- Flawless Zero Trust microsegmentation capabilities
- Continuous identity and device posture risk assessments
- Massive, highly reliable global broker network
What we don't like
- Enterprise-only pricing is prohibitive for smaller businesses
- Complex initial architecture and deployment phase
Best for: Large enterprises and highly regulated industries requiring absolute maximum security and complete application cloaking.
Considering Zscaler Private Access vs Perimeter 81? Zscaler is a heavier, pure-play enterprise ZTNA solution requiring comprehensive architectural shifts, whereas Perimeter 81 offers a more hybrid, user-friendly approach that blends SASE capabilities with easier, small-to-mid-market deployment.
An uncompromising, elite Zero Trust architecture that provides ultimate security and microsegmentation for the modern enterprise.
Buy at Zscaler official site#4 Twingate

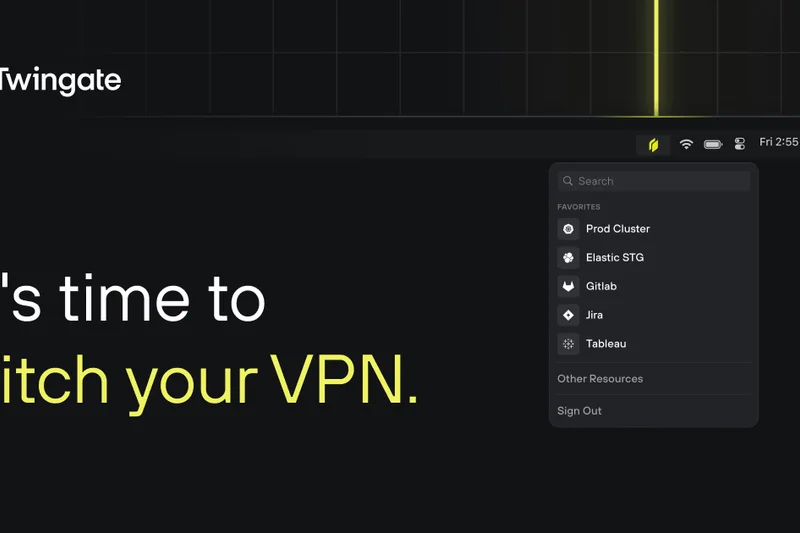
Why we picked it: Twingate earns the #4 spot by offering an exceptionally polished, hardware-free Zero Trust Network Access solution that effectively bridges the gap between complex enterprise SASE platforms and user-friendly team VPNs. Twingate abandons the concept of network-level access entirely, functioning instead as a software-defined perimeter that brokers connections on a strict, per-application basis. This means remote employees can securely access an internal database or cloud staging environment without ever being placed on the broader corporate LAN. Our evaluation highlighted Twingate's brilliant approach to deployment and security. Because it utilizes a reverse proxy architecture via lightweight software 'Connectors' deployed in your cloud or on-premise environments, there is absolutely no need to open inbound ports on your firewall, rendering your infrastructure invisible to external scanning. It scored a 10 in Zero Trust & Advanced Features, boasting granular access controls, native integration with major Identity Providers (IdPs) like Okta and Google Workspace, and highly effective split tunneling that routes only necessary corporate traffic through the secure broker, leaving standard web browsing untouched to preserve bandwidth. End-users benefit from a seamless experience where the Twingate client runs silently in the background, automatically managing access based on SSO authentication without the need to constantly toggle connections on and off. While it lacks the broader web filtering of a full SASE product, Twingate is an outstanding, cost-effective ZTNA solution for modern distributed teams.
Key Specs
- Hardware-free software solution
- No open inbound ports
- Split tunneling
- Granular access controls
- SSO integration
What we like
- Software-only deployment requires no open inbound firewall ports
- Intelligent split tunneling preserves speed and bandwidth
- Granular, application-level Zero Trust access controls
- Client runs silently in the background with seamless SSO
What we don't like
- Does not provide outbound web filtering or malware blocking
- Strictly an access broker, not a traditional site-to-site VPN
Best for: Mid-sized businesses and tech-forward teams looking for a fast, software-defined Zero Trust perimeter without hardware deployment.
Considering Twingate vs NordLayer? Twingate offers a purer, more granular Zero Trust application access model with no open ports, while NordLayer provides a broader suite of traditional cloud VPN features, including dedicated gateways and cloud firewalls.
A highly refined, hardware-free Zero Trust solution that secures application access seamlessly without exposing your network.
Buy at Twingate official site#5 NordLayer
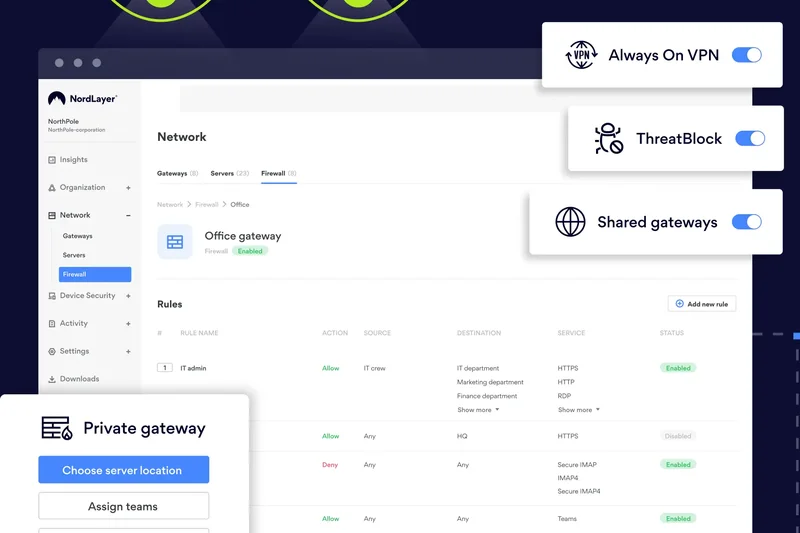
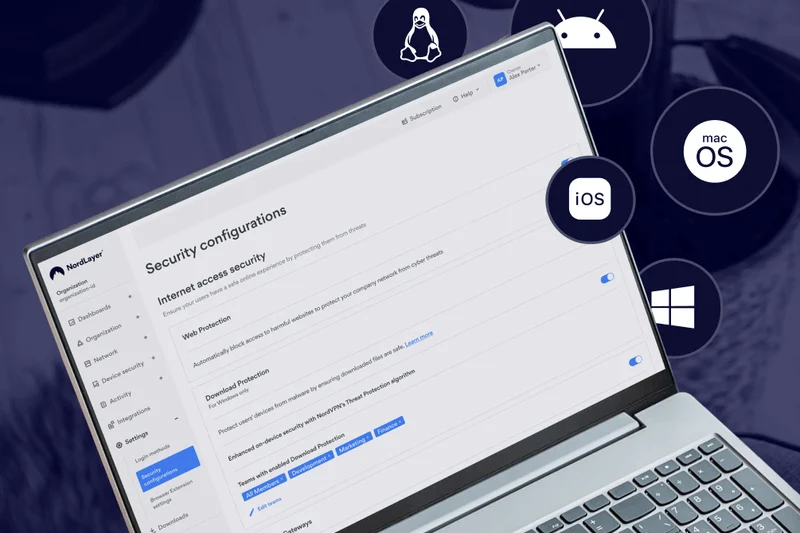
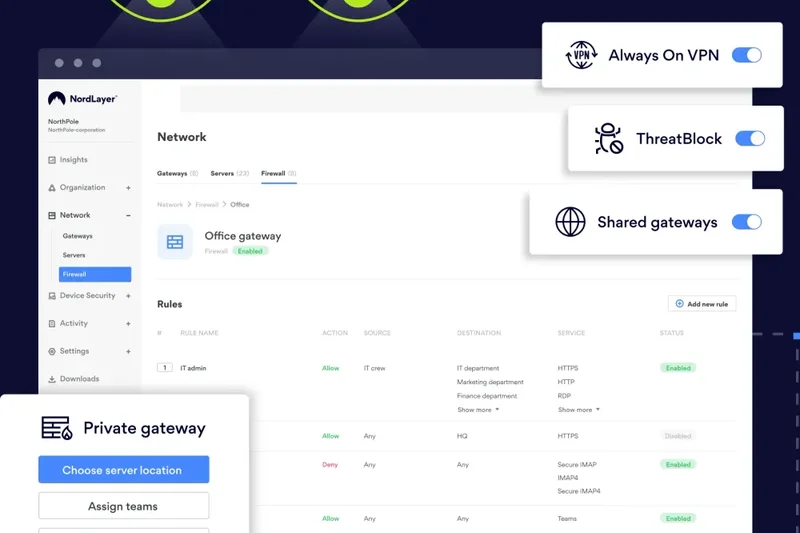
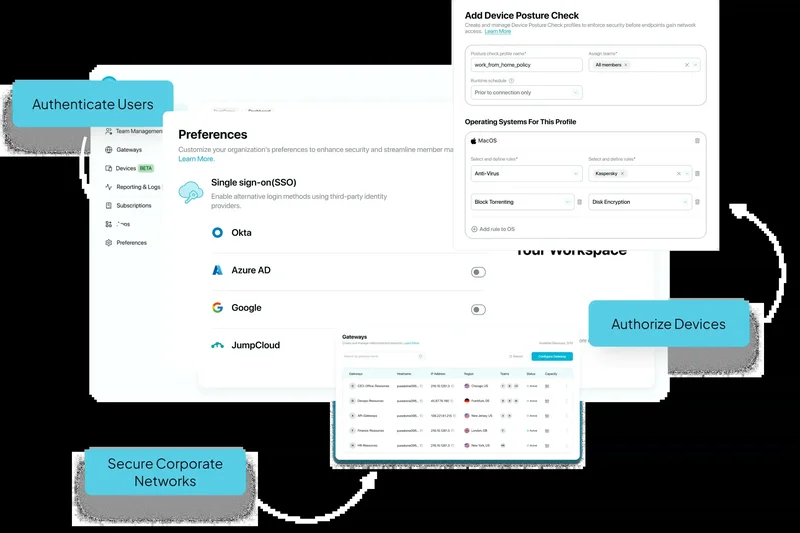
Why we picked it: NordLayer (from Nord Security) takes the #5 position by successfully translating the immense global infrastructure and consumer-friendly design of NordVPN into a robust, highly capable Business VPN and ZTNA hybrid. It is an exceptionally well-rounded platform, scoring highly across the board (9s in Security, Speed, Admin, UX, and Advanced features), making it an ideal choice for businesses transitioning from basic remote access to a more secure cloud perimeter. NordLayer stands out for its flexibility. Administrators can easily deploy dedicated IP addresses and private virtual gateways in dozens of global locations, ensuring remote employees always have a secure, static point of entry to corporate resources. The platform's transition toward SASE is evident in its inclusion of Cloud Firewall (FWaaS) capabilities, DNS filtering, and device posture security checks, which ensure that endpoints are compliant before granting access. The centralized admin control panel is remarkably intuitive, allowing IT managers to provision users, assign dedicated servers, and integrate with SSO providers (Azure AD, Okta) with minimal friction. While it may not offer the extreme, application-level microsegmentation found in pure ZTNA platforms like Zscaler, NordLayer provides an outstanding balance of traditional secure tunneling, modern Zero Trust concepts, and excellent global speeds backed by the proprietary NordLynx (WireGuard-based) protocol. It is highly scalable and predictably priced.
Key Specs
- Zero Trust Network Access
- Cloud Firewall (FWaaS)
- Device Posture Security
- Dedicated IP options
- SSO integration
What we like
- Excellent blend of traditional Cloud VPN and modern ZTNA features
- Highly intuitive centralized admin control panel
- Fast global speeds utilizing the WireGuard-based NordLynx protocol
- Easy deployment of dedicated IP addresses and corporate gateways
What we don't like
- Microsegmentation is not as granular as pure-play enterprise ZTNA
- Pricing can scale up quickly if adding many dedicated gateways
Best for: Growing businesses that need a user-friendly, scalable mix of dedicated IP cloud VPN and modern Zero Trust security features.
Considering NordLayer vs Proton VPN for Business? NordLayer offers superior admin management, deeper SSO integrations, and advanced device posture checks, while Proton VPN focuses more heavily on strict Swiss privacy laws and high-speed 10 Gbps bare-metal servers.
A versatile and highly manageable business VPN that perfectly bridges the gap between dedicated gateways and Zero Trust security.
Buy at NordLayer official site#6 Check Point SASE
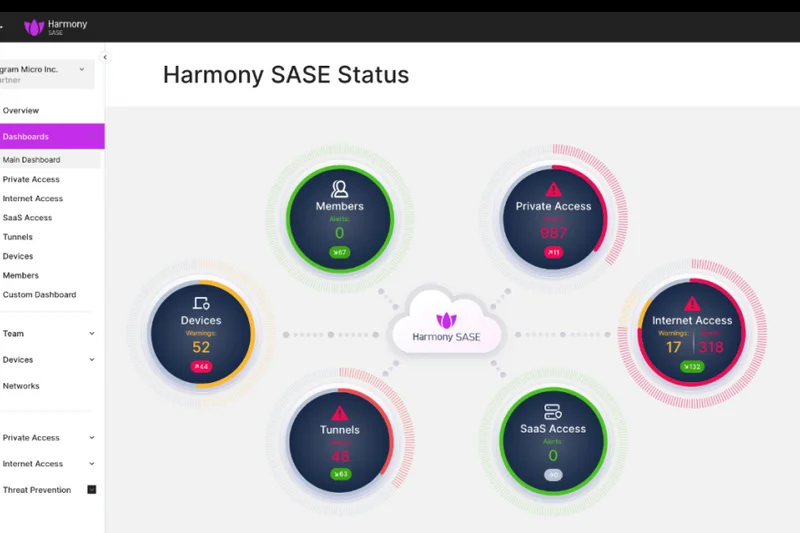
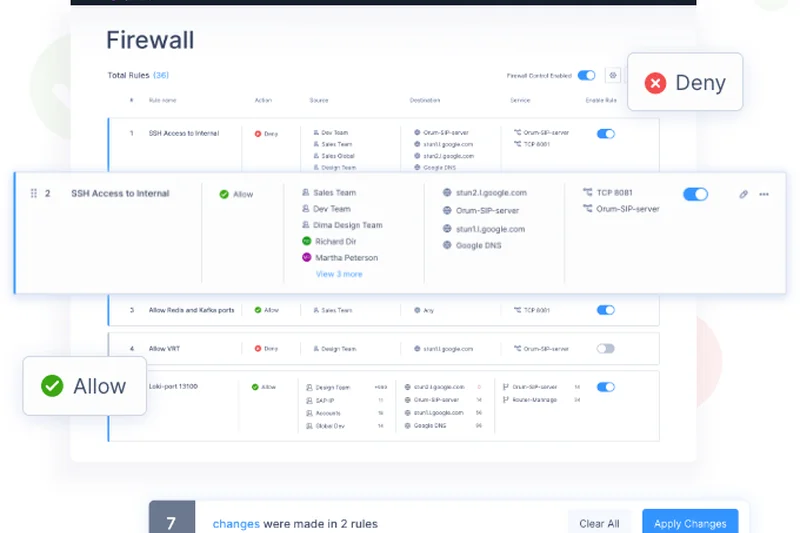
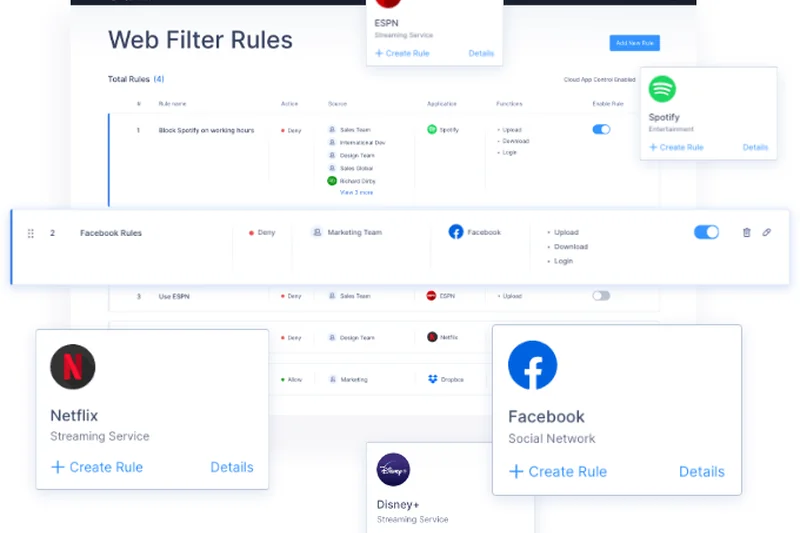
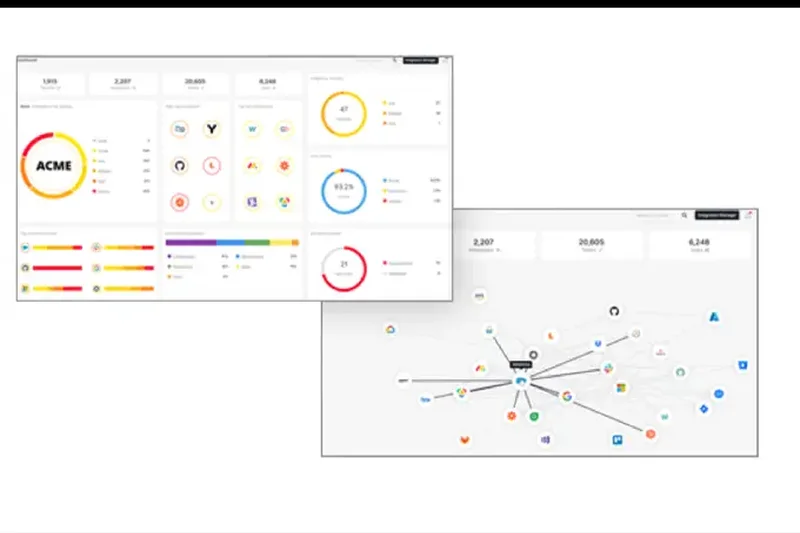
Why we picked it: Check Point SASE secures the #6 spot by offering a comprehensive, enterprise-grade unified security suite. Backed by decades of cybersecurity expertise, this platform fully integrates advanced threat prevention, Zero Trust network access, and global edge routing into a single, cohesive cloud architecture. It scored a perfect 10 in Advanced Features, delivering deep packet inspection, robust data loss prevention, and seamless cloud integrations that appeal directly to security-conscious IT departments.
Key Specs
- Full cloud integration
- Advanced threat prevention
- Zero Trust access
- Unified security suite
- Global PoP network
What we like
- Industry-leading advanced threat prevention engine
- Unified, single-pane-of-glass management console
- Robust global Point of Presence (PoP) network
What we don't like
- Can be overly complex for smaller, non-enterprise teams
- Speed overhead is slightly higher due to deep traffic inspection
Best for: Large organizations seeking a unified SASE platform with top-tier threat prevention and comprehensive security modules.
Considering Check Point SASE vs Netskope Private Access? Both are enterprise heavyweights, but Check Point often integrates more seamlessly for organizations already utilizing their legacy firewall hardware, while Netskope is praised for its pure cloud-native data loss prevention.
A powerhouse SASE platform that wraps Zero Trust access in Check Point's formidable threat prevention technology.
Buy at Check Point official site#7 Perimeter 81
Why we picked it: Perimeter 81 (now part of Check Point) holds the #7 rank, remaining a favorite for mid-market companies seeking to deploy a unified SASE architecture without the crushing complexity of traditional enterprise deployments. It scored a 10 in Zero Trust features, offering excellent always-on VPN capabilities, detailed device posture checks, and integrated DNS filtering to block malicious sites at the edge. The platform's software-defined perimeter allows administrators to easily build custom cloud networks and segment user access visually.
Key Specs
- Unified SASE architecture
- Always-on VPN
- Device posture checks
- DNS Filtering
- Cloud Firewall
What we like
- Visually intuitive network building and segmentation
- Strong always-on VPN and endpoint compliance checks
- Integrated cloud firewall and DNS filtering
What we don't like
- Acquisition transition may affect long-term product roadmaps
- Connection speeds slightly trail WireGuard-native competitors
Best for: Mid-sized organizations wanting robust, visual network segmentation and SASE features without enterprise-level complexity.
Considering Perimeter 81 vs Tailscale? Perimeter 81 provides a more traditional, centrally managed hub-and-spoke cloud network with integrated firewalls, whereas Tailscale focuses purely on decentralized, high-speed peer-to-peer mesh connectivity.
An accessible, feature-rich ZTNA and SASE platform with excellent administrative visibility and network segmentation.
Buy at Perimeter 81 official site#8 Netskope Private Access
Why we picked it: Netskope Private Access comes in at #8, distinguished by its exceptional focus on data protection and continuous risk assessment. As a pure-play ZTNA solution, it completely replaces legacy VPNs by using identity-aware proxies to grant access. Scoring a 10 in Security and Advanced Features, Netskope shines with its integrated Data Loss Prevention (DLP) capabilities, ensuring that sensitive corporate data is not only protected from external threats but also governed tightly against internal exfiltration or accidental leaks.
Key Specs
- Zero Trust Network Access
- Identity-aware proxies
- Data Loss Prevention (DLP)
- Continuous risk assessment
- Replaces legacy VPN
What we like
- Elite Data Loss Prevention (DLP) integrations
- Continuous, dynamic risk assessment during active sessions
- Completely cloaks infrastructure from the public web
What we don't like
- High cost and complex implementation for smaller teams
- User experience can feel restrictive due to strict DLP policies
Best for: Enterprises handling highly sensitive IP or compliance data where robust Data Loss Prevention is a mandatory requirement.
Considering Netskope vs Zscaler? Both offer elite enterprise ZTNA, but Netskope's deeply integrated inline DLP and Cloud Access Security Broker (CASB) features give it an edge for strict data governance use-cases.
A highly advanced ZTNA solution that pairs secure access with unparalleled data loss prevention and risk assessment.
Buy at Netskope official site#9 Appgate SDP
Why we picked it: Appgate SDP secures #9 as a highly robust Software-Defined Perimeter solution. It utilizes a unique single-packet authorization (SPA) technology that keeps infrastructure completely invisible to port scanners while allowing authenticated users to connect dynamically. It scored a 10 in Security, offering identity-centric access that adjusts in real-time based on the user's environment, making it an excellent choice for complex, multi-cloud enterprise architectures where dynamic risk assessment is critical.
Key Specs
- Zero Trust access
- Identity-centric security
- Dynamic risk assessment
- Concurrent access to multiple environments
- Single-packet authorization
What we like
- Single-packet authorization (SPA) hides infrastructure perfectly
- Dynamic, context-aware risk assessment policies
- Excellent concurrent access routing across multiple cloud environments
What we don't like
- Admin interface is highly technical and complex
- Network footprint is smaller than top-tier SASE competitors
Best for: Complex enterprise environments requiring dynamic, identity-centric access control across multiple hybrid cloud deployments.
Considering Appgate SDP vs Twingate? Appgate offers deeper enterprise integrations and dynamic risk policy adjustments, while Twingate provides a vastly simpler, more streamlined deployment experience for mid-market teams.
A highly secure, technically sophisticated software-defined perimeter that excels in complex, multi-cloud enterprise environments.
Buy at Appgate official site#10 Jamf Connect (formerly Wandera)
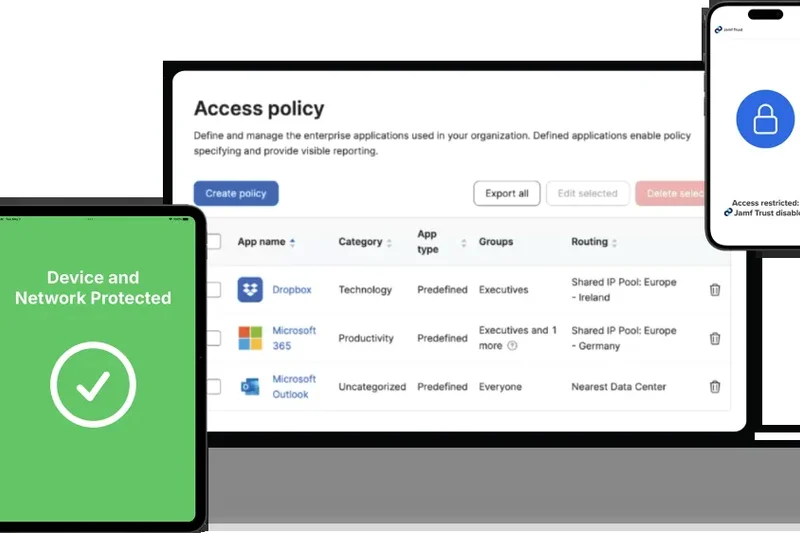
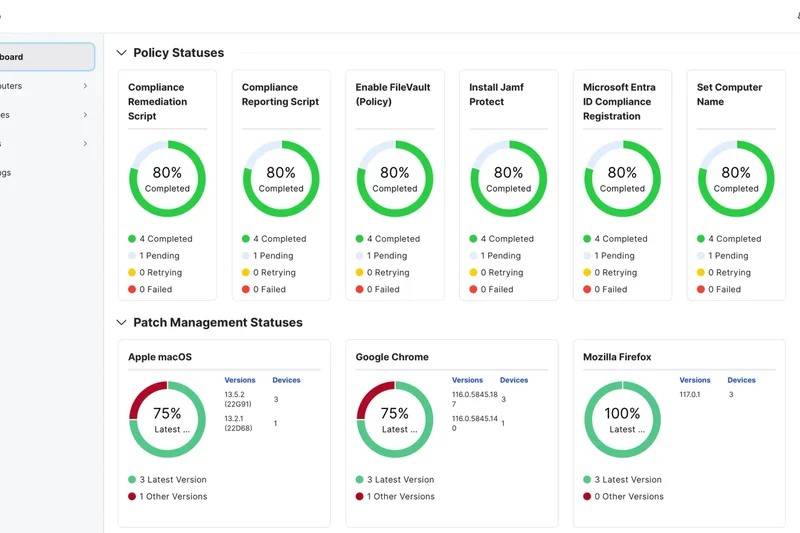
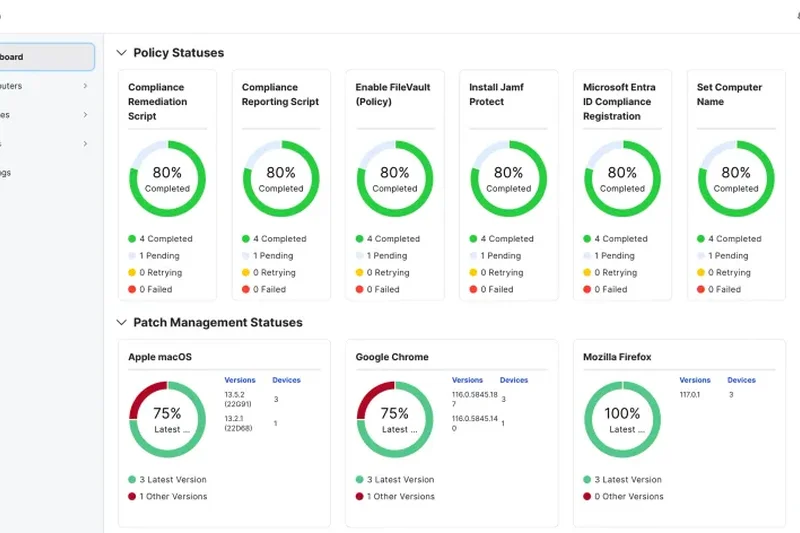
Why we picked it: Jamf Connect (incorporating legacy Wandera technology) rounds out the top 10 as the definitive ZTNA solution for Apple-centric organizations. Scoring highly in User UX (9) and Admin Tools (9), it provides seamless cloud identity provisioning and microsegmentation specifically optimized for macOS and iOS devices. The platform integrates deep threat defense, ensuring mobile and desktop endpoints are secure before granting Zero Trust access to corporate resources, all while providing a native, frictionless experience for Apple users.
Key Specs
- Optimized for Apple devices
- Zero Trust Network Access
- Cloud identity provisioning
- Threat defense integration
- Microsegmentation
What we like
- Flawless integration and optimization for the Apple ecosystem
- Combines ZTNA with robust endpoint threat defense
- Seamless cloud identity and passwordless provisioning
What we don't like
- Less compelling for heavily Windows or Linux-based workforces
- Reporting capabilities could be more comprehensive
Best for: Apple-centric organizations and schools needing seamless identity provisioning and ZTNA optimized for macOS and iOS.
Considering Jamf Connect vs Cisco Secure Client? Jamf provides a vastly superior, native experience for Mac and iOS fleets, whereas Cisco offers broader, deeply entrenched support for mixed-OS enterprise environments.
The absolute best Zero Trust and identity provisioning platform for organizations operating heavily within the Apple ecosystem.
Buy at Jamf official site#11 GlobalProtect
Why we picked it: GlobalProtect by Palo Alto Networks is a formidable enterprise VPN/ZTNA hybrid, scoring a 10 in Security. It extends Palo Alto's industry-leading next-gen firewall security policies directly to remote endpoints, offering advanced threat prevention and granular traffic filtering. It is highly recommended for enterprises already invested in the Palo Alto ecosystem, though its pricing and client weight keep it out of the top 10.
Key Specs
- Next-gen firewall integration
- Advanced threat prevention
- Consistent security policies on/off network
- Cookie or certificate-based auth
- Granular traffic filtering
What we like
- Flawless integration with Palo Alto Next-Gen Firewalls
- Uncompromising endpoint threat prevention
- Consistent security policies regardless of user location
What we don't like
- The client can be resource-heavy on older endpoints
- Requires existing investment in Palo Alto infrastructure to maximize value
Best for: Large enterprises heavily invested in Palo Alto Networks infrastructure needing consistent remote security policies.
Considering GlobalProtect vs FortiClient? Both excel when paired with their respective hardware firewalls; GlobalProtect generally offers more refined ZTNA policy management, while FortiClient is deeply integrated into the Fortinet fabric.
An elite, highly secure remote access client that perfectly extends Palo Alto's next-gen firewall capabilities to remote workers.
Buy at Palo Alto Networks official site#12 NetMotion Mobility
Why we picked it: NetMotion Mobility (by Absolute Software) is uniquely engineered to provide unbreakable connections, particularly over unstable cellular networks. Scoring a 9 in Speed and Admin Tools, it utilizes traffic optimization to ensure applications don't drop when field workers switch between LTE, 5G, and Wi-Fi. It offers deep analytics and reliable policy enforcement, making it the top choice for emergency services and highly mobile field workforces.
Key Specs
- Unbreakable mobile connections
- Traffic optimization
- Deep visibility and analytics
- Policy enforcement
- Optimized for cellular networks
What we like
- Unbreakable session persistence across changing cellular networks
- Excellent traffic optimization for low-bandwidth situations
- Deep visibility into mobile workforce diagnostics
What we don't like
- Overkill and expensive for standard work-from-home desk employees
- Interface feels slightly dated compared to modern SASE peers
Best for: Field workers, emergency responders, and mobile fleets that require unbroken connections across unstable cellular networks.
Considering NetMotion vs standard VPNs? Standard VPNs drop connections when switching from Wi-Fi to cellular, whereas NetMotion maintains session persistence seamlessly.
The undisputed champion for mobile workforces requiring persistent, unbreakable VPN connections over unstable cellular networks.
Buy at Absolute official site#13 Banyan Security
Why we picked it: Banyan Security offers a highly transparent ZTNA solution that emphasizes device trust and continuous authorization. Scoring a 9 in Security, it utilizes a least-privilege access model that can be deployed on-premise or in the cloud. Its strength lies in its transparent user experience and ability to continuously evaluate endpoint health before granting access, though it lacks the massive global footprint of larger competitors.
Key Specs
- Device trust integration
- Least privilege access
- Continuous authorization
- Deployable on-prem or cloud
- Transparent user experience
What we like
- Excellent continuous authorization and device trust integration
- Flexible deployment (on-premise or cloud-native)
- Transparent, frictionless experience for end-users
What we don't like
- Global network infrastructure is smaller than Tier-1 providers
- Requires careful configuration of device trust policies
Best for: Organizations seeking a flexible, device-trust-centric ZTNA solution that works well across hybrid cloud deployments.
Considering Banyan vs Twingate? Both offer excellent ZTNA, but Banyan leans slightly more into continuous device trust evaluation, while Twingate focuses heavily on ease of deployment and zero-config setup.
A strong, highly flexible ZTNA platform that prioritizes continuous authorization and comprehensive endpoint device trust.
Buy at Banyan Security official site#14 Proton VPN for Business



Why we picked it: Proton VPN for Business brings the company's renowned Swiss privacy standards and strict no-logs policy to the corporate sector. Scoring a 9 in Security and Speed, it leverages high-speed 10 Gbps bare-metal servers to deliver excellent performance. While it lacks advanced ZTNA microsegmentation (scoring 5 in Advanced), its dedicated IP options, NetShield ad-blocker, and high value make it superb for privacy-conscious small businesses.
Key Specs
- Strict no-logs policy
- Swiss privacy laws
- High-speed 10 Gbps servers
- Dedicated server & IP options
- NetShield Ad-blocker
What we like
- Unimpeachable Swiss privacy jurisdiction and strict no-logs policy
- Extremely fast 10 Gbps bare-metal server network
- Excellent built-in NetShield malware and ad-blocker
What we don't like
- Lacks advanced Zero Trust microsegmentation and identity policies
- Admin tools are relatively basic compared to enterprise SASE
Best for: Privacy-centric small businesses and journalism outfits requiring strict no-logs security and high-speed encrypted tunnels.
Considering Proton VPN vs NordLayer? Proton focuses heavily on bare-metal privacy and raw speed, while NordLayer offers a much more robust administrative dashboard and a stepping stone toward Zero Trust.
A fast, highly secure business VPN backed by Swiss privacy laws, ideal for teams prioritizing data anonymity over complex ZTNA.
Buy at Proton official site#15 GoodAccess
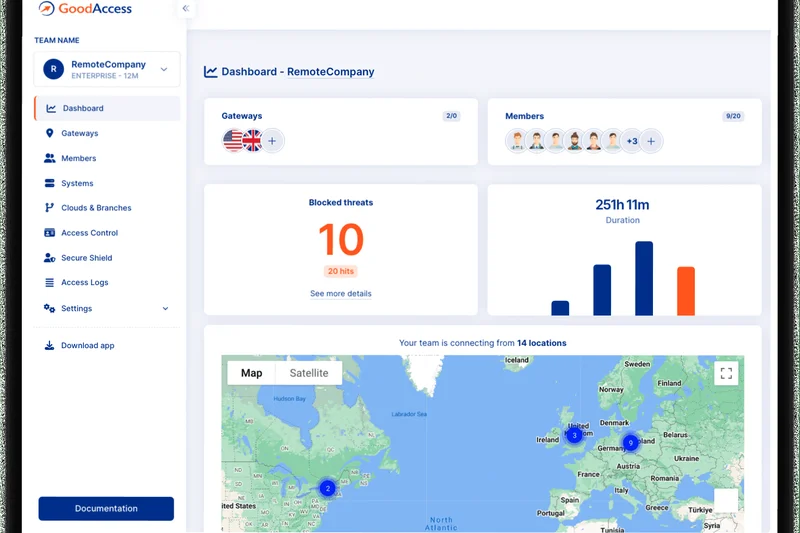
Why we picked it: GoodAccess is a highly accessible Cloud VPN and ZTNA platform that excels at providing static dedicated IPs and cloud firewall capabilities for small to mid-sized teams. Scoring an 8 across Security, Admin, UX, and Value, it allows companies to easily whitelist corporate IPs for SaaS applications while enforcing identity and access management. It is a highly practical, plug-and-play security layer.
Key Specs
- Static dedicated IP
- Cloud firewall
- Identity and access management
- Zero Trust architecture
- DNS filtering
What we like
- Very easy deployment of static dedicated IP addresses
- Straightforward identity and access management
- Solid DNS filtering and cloud firewall capabilities
What we don't like
- Network footprint is smaller than top competitors
- Connection speeds are solid but rarely class-leading
Best for: Small to mid-sized businesses needing a simple way to deploy static IPs and basic Zero Trust access for remote workers.
Considering GoodAccess vs UTunnel? GoodAccess provides a slightly more refined, fully managed cloud experience, whereas UTunnel offers more flexibility for hybrid on-premise deployments.
A highly practical, easy-to-deploy cloud VPN that provides static IPs and solid access management for growing teams.
Buy at GoodAccess official site#16 Cisco Secure Client (AnyConnect)
Why we picked it: Cisco Secure Client (formerly AnyConnect) remains an absolute titan in enterprise security, scoring a 10 in Security protocols. It provides highly scalable, multi-factor authenticated remote access with deep endpoint posture assessments and telemetry. However, its lower speed scores and notoriously rigid User UX (scoring 5) keep it lower on our list for modern, agile remote teams.
Key Specs
- Seamless Cisco infrastructure integration
- Endpoint posture assessment
- Highly scalable
- Multi-factor authentication
- Telemetry and threat defense
What we like
- Industry-standard security protocols and endpoint assessment
- Massively scalable for hundreds of thousands of users
- Deep integration with the broader Cisco security ecosystem
What we don't like
- User experience can be frustrating and clunky
- High cost and complex licensing structures
Best for: Massive global enterprises and government entities already deeply entrenched in Cisco network infrastructure.
Considering Cisco Secure Client vs GlobalProtect? Both are legacy firewall giants transitioning to ZTNA; Cisco offers broader legacy compatibility, while Palo Alto's GlobalProtect often provides slightly better threat prevention telemetry.
The quintessential enterprise VPN client, offering bulletproof security and scale at the cost of end-user experience.
Buy at Cisco official site#17 Surfshark for Teams
Why we picked it: Surfshark for Teams leverages its highly successful consumer infrastructure to provide a cost-effective, unlimited-connection security suite for small businesses. Scoring a 9 in Speed, Network, and UX, it includes CleanWeb ad blocking, integrated antivirus, and data breach alerts. While it lacks true administrative deployment tools and ZTNA (scoring 6 and 5 respectively), its immense value is undeniable.
Key Specs
- Unlimited simultaneous connections
- CleanWeb ad blocker
- Antivirus included
- Data breach alerts
- Identity theft protection
What we like
- Allows unlimited simultaneous device connections per user
- Excellent high-speed global server network
- Includes added value like antivirus and breach alerts
What we don't like
- Lacks centralized deployment and advanced ZTNA policies
- Admin console is very basic compared to true B2B VPNs
Best for: Small teams, freelancers, and bootstrapped startups looking for high-speed, affordable privacy coverage across all devices.
Considering Surfshark for Teams vs ExpressVPN? Surfshark offers unlimited connections and a slightly better team billing setup, while ExpressVPN generally commands a premium for marginally faster raw speeds.
An exceptionally high-value, fast VPN suite for small teams that require basic privacy and unlimited device coverage.
Buy at Surfshark official site#18 FortiClient
Why we picked it: FortiClient by Fortinet is a robust Endpoint Security and VPN agent that integrates perfectly with the Fortinet ecosystem. It scores a 9 in Security and Advanced Features by offering a strong blend of SSL/IPsec VPN, endpoint protection (EPP), and Zero Trust access. However, like Cisco, its lower speed (6) and rigid UX (6) make it better suited for strict corporate compliance rather than modern flexibility.
Key Specs
- Fortinet ecosystem integration
- SSL and IPsec VPN
- Endpoint protection (EPP)
- Zero Trust network access
- Vulnerability scanning
What we like
- Deep, native integration with Fortinet hardware and fabrics
- Strong built-in endpoint vulnerability scanning
- Reliable SSL and IPsec VPN tunneling
What we don't like
- Client can feel heavy and intrusive to end-users
- Requires Fortinet infrastructure for optimal management
Best for: Enterprises utilizing Fortinet hardware looking to extend their security fabric to remote endpoints.
Considering FortiClient vs Cisco AnyConnect? Both serve similar enterprise infrastructure needs; FortiClient includes stronger native vulnerability scanning, while Cisco is more universally deployed.
A highly secure, compliance-driven endpoint agent that excels within established Fortinet security architectures.
Buy at Fortinet official site#19 UTunnel VPN
Why we picked it: UTunnel VPN is a highly flexible solution that allows businesses to deploy secure cloud VPNs or ZTNA architectures either on-premise or in the cloud. It scores an 8 in Admin Tools and Advanced features, offering policy-based access control and a straightforward web-based admin UI. It's a highly rated, affordable option for IT teams that want more manual control over their server deployments.
Key Specs
- Deploy on-prem or cloud
- OpenVPN and IPsec
- Policy-based access control
- Zero Trust Application Access
- Web-based admin
What we like
- Excellent flexibility to deploy on-premise or via cloud providers
- Straightforward policy-based access control management
- Very affordable pricing structure
What we don't like
- Does not offer the massive managed edge network of larger rivals
- Slightly steeper initial setup curve for self-hosted options
Best for: Mid-market IT teams wanting an affordable, flexible VPN/ZTNA solution that can be deployed on their own cloud infrastructure.
Considering UTunnel vs OpenVPN Access Server? UTunnel provides a much more modern, user-friendly wrapper for deploying OpenVPN and IPsec servers, saving significant administrative time.
A highly capable and affordable solution for teams seeking flexible, self-managed cloud or on-premise secure access.
Buy at UTunnel official site#20 Windscribe ScribeForce
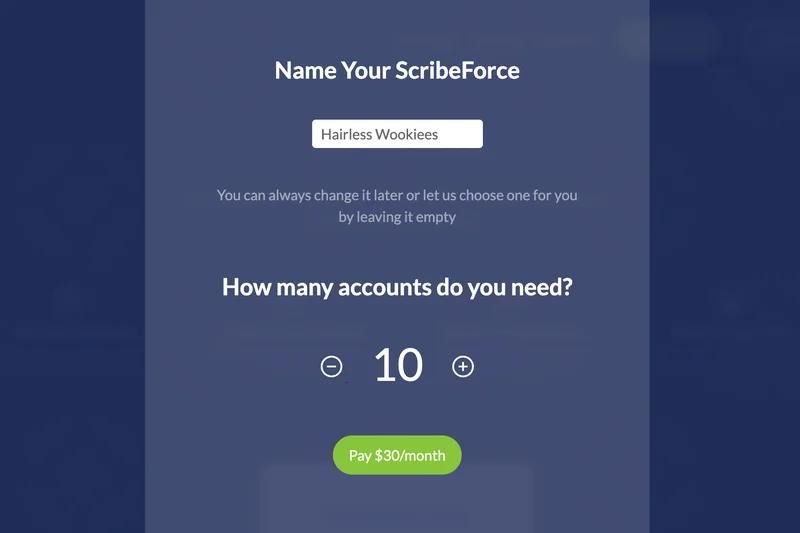
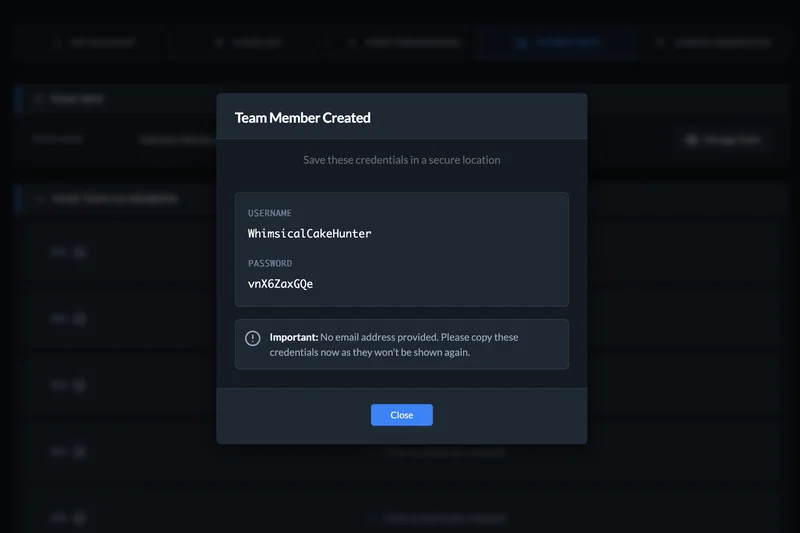
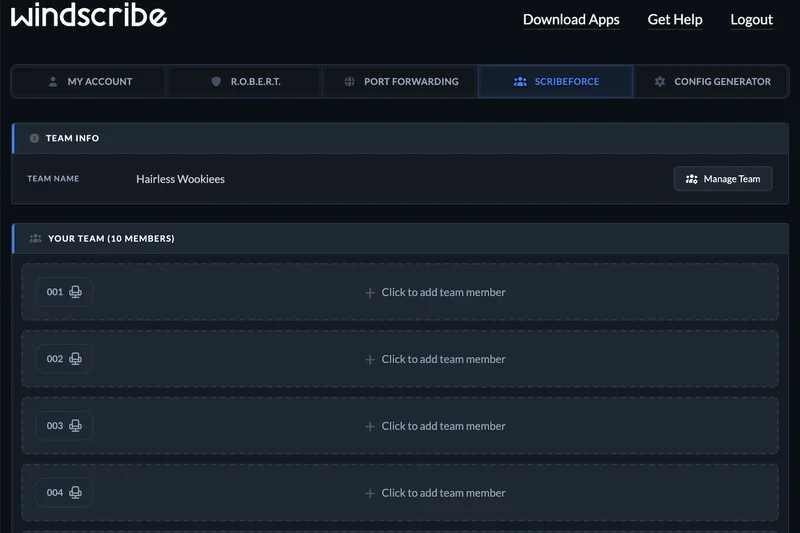
Why we picked it: Windscribe ScribeForce is the undisputed champion of budget-friendly team VPNs, scoring a perfect 10 in Value. At just $3/user/month, it provides centralized billing, configurable team access, and the powerful ROBERT malware/ad blocker. While it lacks enterprise ZTNA (scoring 5 in Advanced), its unlimited connections and strict no-logs policy make it an incredible bargain for basic corporate privacy.
Key Specs
- Centralized billing
- ROBERT malware/ad blocker
- Unlimited connections
- No identifying logs
- Configurable team access
What we like
- Unbeatable value at $3 per user per month
- Excellent ROBERT customizable DNS filtering and ad blocking
- Allows unlimited simultaneous connections
What we don't like
- No Zero Trust microsegmentation or advanced identity policies
- Admin panel is very basic, lacking deep telemetry
Best for: Bootstrapped startups and very small businesses needing essential encrypted browsing and team billing on a tight budget.
Considering Windscribe ScribeForce vs CyberGhost VPN? Windscribe offers a superior, highly customizable DNS filtering tool (ROBERT) and better team pricing, making it the better choice for small businesses.
An incredibly cost-effective, no-logs team VPN featuring powerful customizable DNS filtering and unlimited connections.
Buy at Windscribe official site#21 Ivanti Connect Secure

Why we picked it: Ivanti Connect Secure (formerly Pulse Secure) is a massively scalable Enterprise VPN and ZTNA platform. It scores a 9 in Security and 8 in Admin Tools, offering robust always-on VPN, clientless web access, and strict endpoint compliance checks. However, its lower speed scores (6) and highly rigid enterprise UX (5) limit its appeal to organizations primarily focused on strict legacy compliance.
Key Specs
- Always-on VPN
- Clientless access
- Endpoint compliance checks
- Seamless SSO
- Scalable for massive remote workforces
What we like
- Proven ability to scale for massive, global remote workforces
- Strong endpoint compliance and posture validation
- Excellent clientless web access options
What we don't like
- Client software feels outdated and can be finicky
- Complex enterprise licensing and management overhead
Best for: Large enterprises and government agencies requiring massively scalable, highly compliant remote access infrastructure.
Considering Ivanti Connect Secure vs Cisco Secure Client? Both are legacy enterprise staples; Ivanti often provides slightly better clientless access portals, while Cisco has a broader integration ecosystem.
A heavy-duty, highly scalable enterprise remote access solution with strict endpoint compliance capabilities.
Buy at Ivanti official site#22 PureDome VPN
Why we picked it: PureDome VPN (by PureVPN) is a dedicated business solution designed for quick deployment and straightforward management. Scoring an 8 in Value and Network, it provides dedicated IP addresses, a centralized admin panel, and AES-256 encryption. It serves as a solid, middle-of-the-road cloud VPN for small businesses, though it lacks the advanced ZTNA polish of higher-ranked competitors.
Key Specs
- Dedicated IPs
- Centralized admin panel
- AES-256 encryption
- Identity-based access
- Quick deployment
What we like
- Straightforward centralized admin panel
- Easy provisioning of dedicated IP addresses
- Quick and painless deployment process
What we don't like
- Speeds are average compared to WireGuard-native platforms
- Zero Trust features are relatively basic
Best for: Small to medium businesses looking for a straightforward, quick-to-deploy VPN with dedicated IP capabilities.
Considering PureDome vs GoodAccess? Both target similar markets; GoodAccess offers slightly better built-in cloud firewall features, while PureDome has a somewhat broader underlying consumer network.
A reliable, easy-to-manage business VPN that provides essential dedicated IP access and basic team administration.
Buy at PureDome official site#23 TorGuard Business VPN

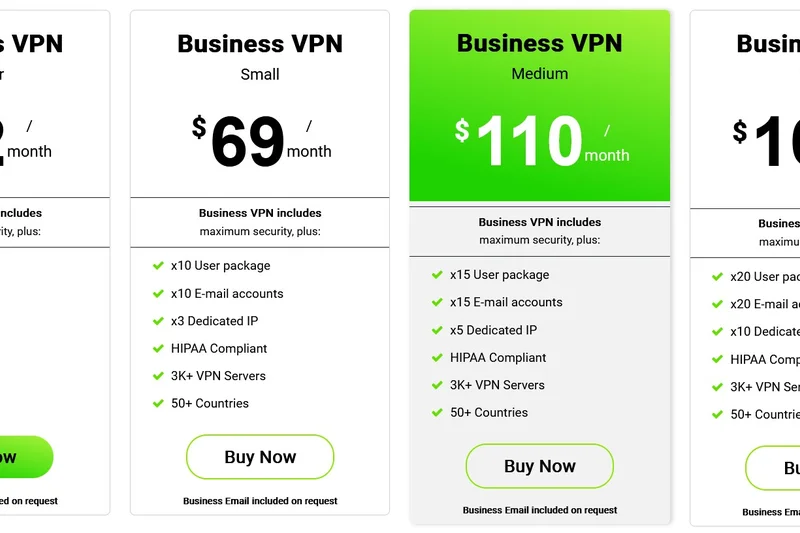
Why we picked it: TorGuard Business VPN is tailored for organizations that require stealth and high-level anonymity. Scoring an 8 in Security and Speed, it provides dedicated VPN IPs, Stealth VPN protocols to bypass strict regional firewalls, and includes encrypted email. It's an excellent niche choice for teams operating in restrictive regions, though its UX (6) and Admin (7) are less refined.
Key Specs
- Dedicated VPN IP
- Stealth VPN protocols
- Encrypted email included
- No logs policy
- 24/7 dedicated account manager
What we like
- Stealth protocols are excellent for bypassing restrictive national firewalls
- Includes dedicated IPs and encrypted email accounts
- 24/7 dedicated account manager for business tiers
What we don't like
- Client interface is highly technical and dated
- Lacks modern SASE and Zero Trust architecture
Best for: Journalists, remote teams in restrictive countries, and privacy-focused businesses needing stealth capabilities.
Considering TorGuard vs Astrill VPN? Both excel at bypassing strict firewalls (like the Great Firewall of China); TorGuard offers better included business extras like encrypted email and dedicated IPs.
A highly secure, stealth-focused VPN ideal for businesses operating in heavily censored or restrictive internet environments.
Buy at TorGuard official site#24 Hide.me Business
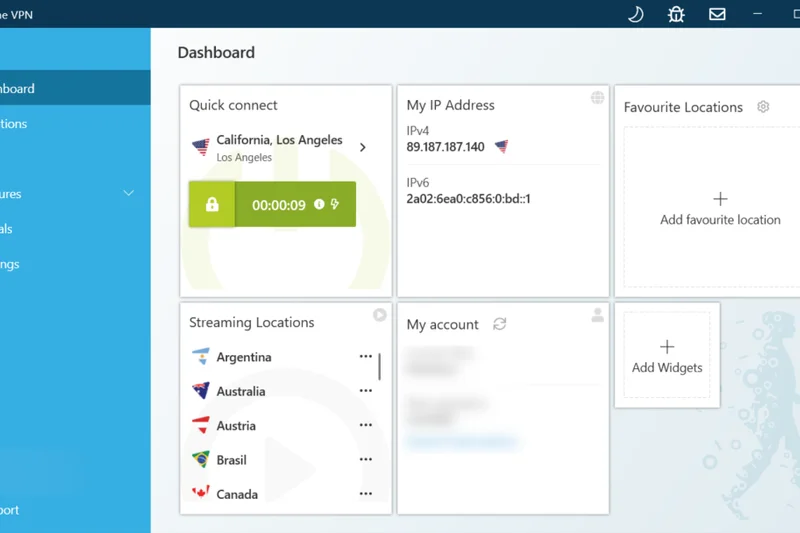
Why we picked it: Hide.me Business is a highly secure, privacy-centric VPN that operates self-managed servers to guarantee strict no-logs compliance. Scoring an 8 in Security and Speed, it supports WireGuard and features "Stealth Guard" functionality. It offers custom team pricing and strong IPv6 support, making it a technically sound choice for small teams prioritizing data sovereignty.
Key Specs
- Independently audited no-logs
- WireGuard support
- Stealth Guard
- IPv6 support
- Self-managed servers
What we like
- Strict, independently audited no-logs policy
- Company owns and manages all its own servers for better security
- Strong WireGuard performance and IPv6 support
What we don't like
- Business administration features are quite barebones
- Smaller overall server network than major competitors
Best for: Small technical teams and privacy purists who value self-managed server infrastructure and audited no-logs policies.
Considering Hide.me vs Mullvad? Mullvad offers even more extreme privacy with anonymous accounts, while Hide.me provides a slightly more traditional team management structure.
A technically robust, highly private VPN utilizing self-managed servers to ensure maximum data security for small teams.
Buy at Hide.me official site#25 SonicWall Secure Mobile Access (SMA)


Why we picked it: SonicWall Secure Mobile Access (SMA) is a reliable Secure Access Gateway designed to integrate tightly with existing SonicWall firewalls. Scoring an 8 in Security and Admin Tools, it provides context-aware access and strong endpoint control. However, its low Speed (6) and UX (5) scores reflect its legacy architecture, making it suitable mainly for current SonicWall customers.
Key Specs
- Endpoint control
- Advanced authentication
- Context-aware access
- SSL VPN
- Integrates with SonicWall firewalls
What we like
- Excellent integration with existing SonicWall firewall deployments
- Strong endpoint control and context-aware authentication
- Highly reliable SSL VPN connections
What we don't like
- Client software is dated and not user-friendly
- Requires existing SonicWall hardware for best results
Best for: Enterprises currently utilizing SonicWall network hardware that need to extend secure access to mobile workforces.
Considering SonicWall SMA vs FortiClient? Both are vendor-specific; FortiClient generally offers a slightly more modernized ZTNA approach, but choice depends entirely on your existing hardware vendor.
A dependable, compliance-focused secure access gateway that works best when paired with SonicWall hardware.
Buy at SonicWall official site#26 Astrill VPN Business

Why we picked it: Astrill VPN Business is a high-end, premium-priced VPN known for its unparalleled ability to bypass regional restrictions using its proprietary StealthVPN protocol. Scoring a 9 in Security and 8 in Speed, it offers VIP servers, multi-hop routing, and port forwarding. However, its high price and poor UX/Value scores make it a niche tool for specialized international access.
Key Specs
- StealthVPN protocol
- Smart Mode for regional restrictions
- Port forwarding
- VIP servers
- Multi-hop routing
What we like
- Unmatched ability to bypass strict national firewalls (e.g., in Asia)
- Advanced multi-hop routing and VIP server options
- Fast proprietary StealthVPN protocol
What we don't like
- Extremely expensive compared to almost all competitors
- User interface is highly technical and unforgiving
Best for: International executives and teams frequently traveling to regions with heavy internet censorship and strict firewalls.
Considering Astrill VPN vs ExpressVPN? Both bypass regional blocks well, but Astrill is more consistently reliable in extreme censorship zones, albeit at a significantly higher price and lower ease-of-use.
An expensive, highly technical VPN that remains the absolute best choice for bypassing heavy international internet censorship.
Buy at Astrill official site#27 ExpressVPN

Why we picked it: ExpressVPN is traditionally a consumer giant, but its incredible speed (10), massive network (10), and flawless UX (10) make it a viable option for very small businesses or executive travelers. Utilizing its proprietary Lightway protocol and TrustedServer (RAM-only) technology, it is incredibly fast and secure. However, it completely lacks centralized business admin tools (scoring 3), making it unmanageable for larger teams.
Key Specs
- Lightway protocol
- Servers in 105 countries
- TrustedServer technology (RAM-only)
- Threat Manager
- Fast global speeds
What we like
- Incredible global speeds via the Lightway protocol
- TrustedServer RAM-only architecture ensures no data is saved
- Flawless, highly intuitive apps for all devices
What we don't like
- No centralized team management or billing dashboard
- No dedicated IP or Zero Trust capabilities
Best for: Solo entrepreneurs, C-suite executives, and digital nomads needing ultra-fast, reliable privacy while traveling.
Considering ExpressVPN vs Surfshark for Teams? Surfshark provides a basic team management console and unlimited connections, making it better for groups, while ExpressVPN is faster for individual use.
An ultra-premium, high-speed consumer VPN that works perfectly for individual executives, but lacks necessary B2B management tools.
Buy at ExpressVPN official site#28 TunnelBear for Teams


Why we picked it: TunnelBear for Teams takes a highly approachable, user-friendly angle to corporate privacy. Scoring a 9 in UX and 8 in Security, it offers centralized team management, a VigilantBear kill switch, and GhostBear obfuscation, all wrapped in a uniquely playful interface. Annual independent audits prove its security chops, though it lacks advanced business network features.
Key Specs
- Centralized team management
- VigilantBear kill switch
- GhostBear obfuscation
- Annual independent security audits
- AES-256 encryption
What we like
- Extremely user-friendly interface is great for non-technical staff
- Regular, transparent independent security audits
- Solid centralized team billing and management
What we don't like
- Playful branding may not fit strict corporate environments
- Lacks dedicated IPs and advanced ZTNA routing
Best for: Small, non-technical teams and creative agencies that want a highly approachable, easy-to-use privacy solution.
Considering TunnelBear for Teams vs Windscribe ScribeForce? Windscribe offers better technical features and ad-blocking at a lower price, while TunnelBear offers a much gentler learning curve for non-technical users.
A highly audited, incredibly user-friendly team VPN that makes basic corporate privacy accessible to non-technical staff.
Buy at TunnelBear official site#29 VyprVPN for Business
Why we picked it: VyprVPN for Business utilizes its proprietary Chameleon protocol to defeat VPN blocking and deep packet inspection. Scoring an 8 in Security and Network, it includes a NAT firewall and a dedicated account manager. While it is a solid, privacy-respecting VPN with its own server network, its pricing structure and lack of modern ZTNA features limit its broader appeal.
Key Specs
- Chameleon protocol
- Dedicated account manager
- Global server network
- NAT firewall included
- No-logs policy
What we like
- Chameleon protocol effectively defeats VPN blocking
- Company owns its own hardware and server network
- Includes a built-in NAT firewall
What we don't like
- Pricing structure is somewhat rigid
- Lacks modern microsegmentation and identity features
Best for: Small to medium businesses that require reliable connection obfuscation and value a provider that owns its own hardware.
Considering VyprVPN vs TorGuard? Both offer excellent obfuscation protocols; VyprVPN has slightly more polished client apps, while TorGuard offers more flexible dedicated IP options.
A solid, hardware-owning VPN provider featuring strong obfuscation protocols to bypass deep packet inspection.
Buy at VyprVPN official site#30 OpenVPN Access Server
Why we picked it: OpenVPN Access Server is the classic, open-source foundation of secure remote access. Scoring an 8 in Security, it allows IT teams to deploy highly customizable VPN servers on-premise or in the cloud. It features granular access controls and LDAP/RADIUS support. However, its manual deployment nature (Admin: 7) and lower speeds (6) make it best for highly technical networking teams.
Key Specs
- Open-source foundation
- On-premise or cloud deployment
- Granular access controls
- LDAP and RADIUS support
- Web-based admin UI
What we like
- Incredibly customizable open-source foundation
- Excellent support for traditional LDAP and RADIUS authentication
- Can be deployed entirely on your own infrastructure
What we don't like
- Requires significant technical expertise to deploy and maintain
- OpenVPN protocol is slower than modern WireGuard alternatives
Best for: Highly technical IT departments and sysadmins who want total control over their self-hosted VPN infrastructure.
Considering OpenVPN Access Server vs UTunnel? UTunnel provides a much more modern, user-friendly wrapper for deploying OpenVPN and IPsec servers, saving significant administrative time.
The highly customizable, traditional standard for self-hosted VPNs, best suited for experienced network administrators.
Buy at OpenVPN official site#31 TSplus Remote Access

Why we picked it: TSplus Remote Access functions as a VPN alternative, focusing on web-based application publishing and remote desktop delivery. Scoring a 9 in Value, it allows businesses to self-host applications and deliver them via a web browser, natively limiting lateral network movement. While not a traditional VPN (Network: 4), it is a highly cost-effective remote access solution for legacy apps.
Key Specs
- VPN alternative
- Web-based application publishing
- Self-hosted solution
- Active Directory integration
- Limits lateral movement
What we like
- Excellent, cost-effective alternative to traditional VPNs
- Allows legacy applications to be published directly to web browsers
- Lifetime license pricing offers great long-term value
What we don't like
- Not a traditional VPN; does not secure general internet traffic
- Requires managing your own application hosting servers
Best for: Small to mid-sized businesses looking to securely publish legacy desktop applications to remote workers via web browsers.
Considering TSplus vs a standard VPN? TSplus is designed specifically for remote desktop and application delivery, whereas a VPN secures the entire network connection.
A highly cost-effective, web-based remote access and application delivery tool that serves as a smart alternative to full VPNs.
Buy at TSplus official site#32 Mullvad VPN
Why we picked it: Mullvad VPN is the absolute pinnacle of consumer privacy, scoring a 10 in Security and 9 in Speed. It requires no email to create an account and operates with total transparency. However, its deliberate lack of any centralized management, logging, or team features results in an Admin score of 2, making it practically impossible to manage as a corporate IT solution.
Key Specs
- Anonymous accounts (no email required)
- WireGuard protocol
- Strict no-logs policy
- Transparent ownership
- Flat pricing
What we like
- Unrivaled commitment to user anonymity and privacy
- Extremely fast and reliable WireGuard implementation
- Transparent ownership and flat, predictable pricing
What we don't like
- Absolutely no team management, billing, or admin features
- Impossible for IT to monitor or enforce usage policies
Best for: Solo investigative journalists, activists, and extreme privacy purists who manage their own security individually.
Considering Mullvad vs Proton VPN for Business? Mullvad offers superior absolute anonymity, but Proton provides the actual administrative tools required to manage a business team.
An incredibly fast and uncompromisingly private VPN that is perfect for individuals but lacks any business management tools.
Buy at Mullvad official site#33 KeepSolid VPN Unlimited Business
Why we picked it: KeepSolid VPN Unlimited Business offers a straightforward team VPN with a personal VPN server and dedicated IP options. Scoring an 8 in Value and 7 in Security, it provides a functional team management console and AES-256 encryption. It is an affordable, middle-tier option, though its lower speed (6) and UX (6) scores keep it near the bottom of the rankings.
Key Specs
- Personal VPN server
- Dedicated IP
- Team management console
- High-speed connections
- AES-256 encryption
What we like
- Affordable pricing with a functional team management console
- Easy to set up a personal VPN server and dedicated IP
- Solid AES-256 encryption
What we don't like
- Speeds are inconsistent compared to top-tier providers
- Client apps are somewhat clunky and visually dated
Best for: Small businesses looking for an affordable way to secure public Wi-Fi access with basic team billing.
Considering KeepSolid vs PureDome? PureDome offers a slightly more modern interface and marginally better connection stability for dedicated IPs.
A budget-friendly, functional business VPN that covers the basics of encryption and team management without standout features.
Buy at KeepSolid official site#34 Private Internet Access (PIA)



Why we picked it: Private Internet Access (PIA) is a highly respected privacy VPN known for its open-source apps and massive global server network. Scoring a 9 in Network and 8 in Security, it offers excellent WireGuard support and dedicated IP options. However, like other consumer-first brands, its lack of dedicated business management tools (Admin: 3) makes it difficult to scale for remote workforces.
Key Specs
- Open-source apps
- Strict no-logs policy
- Dedicated IP options
- WireGuard support
- Unlimited device connections
What we like
- Fully open-source client apps and strict no-logs policy
- Massive global server network ensures reliable connections
- Highly customizable encryption and networking settings
What we don't like
- No dedicated team management or centralized billing portal
- Lacks business-grade access control features
Best for: Solo freelancers and highly technical individuals who want an open-source, highly customizable privacy VPN.
Considering PIA vs Surfshark for Teams? Surfshark provides a slightly better setup for small groups with basic team billing, while PIA offers more deep-level technical customization for individuals.
A highly customizable, open-source VPN with a massive network, best suited for individual power users rather than managed teams.
Buy at PIA official site#35 CyberGhost VPN

Why we picked it: CyberGhost VPN rounds out our list as a popular, user-friendly VPN with a very large global server fleet. Scoring a 9 in Network and 8 in UX, it offers dedicated IP options and NoSpy servers. However, its low Admin score (3) and lack of advanced corporate features (4) relegate it to individual use rather than a cohesive business remote access strategy.
Key Specs
- NoSpy servers
- Dedicated IP options
- Strict no-logs policy
- One-click connection
- Large global server fleet
What we like
- Very large global server footprint
- Highly secure NoSpy servers operated directly by the company
- User-friendly, one-click connection interface
What we don't like
- No B2B administrative dashboard or team deployment tools
- Zero Trust and access control features are nonexistent
Best for: Individual remote workers needing a simple, user-friendly VPN with a vast array of global server choices.
Considering CyberGhost vs ExpressVPN? ExpressVPN provides much faster speeds and a sleeker interface, while CyberGhost often offers cheaper long-term subscriptions for solo users.
A reliable, consumer-friendly VPN with a huge network, but lacking the necessary management tools for corporate deployment.
Buy at CyberGhost official siteBuying Guide
Business VPN Buying Guide 2026
Choosing the right Virtual Private Network (VPN) or Zero Trust Network Access (ZTNA) solution is a critical foundational decision for any organization managing a remote or hybrid workforce. Not all remote access tools are created equal; the architectural and security differences between a legacy corporate VPN and a modern cloud-native Secure Access Service Edge (SASE) platform are vast. This guide breaks down how to match your company's specific security compliance needs, budget, and administrative bandwidth with the right technology.
1. Identify Your User Type & Threat Model
Startups and Small Teams (10-50 users): If you operate a small, distributed team without a dedicated IT security operations center, your priority should be ease of deployment and low administrative friction. Look for modern mesh VPNs or cloud-hosted ZTNA solutions that do not require purchasing dedicated hardware appliances or configuring complex inbound firewall ports. Features like native Single Sign-On (SSO) integration with Google Workspace or Microsoft 365, alongside simple role-based access control (RBAC), are essential for smooth onboarding and offboarding.
Mid-Market to High-Security Enterprise: Organizations handling sensitive customer financial data, strict compliance frameworks (SOC 2, HIPAA, GDPR), or highly proprietary intellectual property require uncompromising security perimeters. Transitioning away from legacy IPsec/SSL VPNs to a full Zero Trust architecture is mandatory in 2026. You should prioritize SASE platforms offering true microsegmentation, continuous device posture checks (ensuring an endpoint's OS is patched and antivirus is active before granting connection), and deep telemetry integration with your SIEM tools.
2. The Paradigm Shift: Legacy VPN vs. Zero Trust (ZTNA)
The cybersecurity industry has decisively shifted from traditional perimeter VPNs to Zero Trust Network Access. A traditional VPN connects a remote user to the entire corporate network via an encrypted tunnel. The fatal flaw is that if an attacker compromises that single user's credentials, they gain the ability to move laterally across your entire internal network. ZTNA, conversely, operates on the strict principle of "never trust, always verify." It connects users directly and exclusively to the specific applications they are authorized to use, rather than the underlying network infrastructure. This dramatically reduces the attack surface and prevents catastrophic lateral movement breaches. For any forward-looking IT strategy, ZTNA is the required standard.
3. Crucial Technical Features to Evaluate
- Encryption & Modern Protocols: Verify the provider utilizes AES-256 or ChaCha20 encryption. For the tunneling protocol, WireGuard is the current gold standard, offering vastly superior connection speeds, instant handshakes, and lower latency compared to legacy protocols like OpenVPN and IPsec, all without sacrificing cryptographic strength.
- Centralized Admin Console & Telemetry: A unified, intuitive dashboard is vital for IT teams. You must have real-time visibility into active user sessions, bandwidth consumption, and blocked security events. Automated user provisioning via SCIM (System for Cross-domain Identity Management) synchronization saves countless administrative hours and prevents orphaned accounts.
- Global Edge Network Infrastructure: If your workforce or client base is international, the provider must maintain dense local Points of Presence (PoPs) to minimize latency overhead. Routing a remote developer in Tokyo through a security gateway in New York just to access a cloud application will severely degrade performance and cause end-user frustration.
4. Common Pitfalls to Avoid
Repurposing Consumer VPNs: Avoid the temptation to repurpose basic, consumer-grade privacy VPNs for corporate team access. While fine for hiding a personal IP at a coffee shop, they completely lack centralized billing, policy management, dedicated static IP addresses, and identity verification, making them unmanageable at scale and useless for securing internal company resources.
Hardware Appliance Lock-in: Be highly wary of legacy networking vendors that force you to purchase expensive, proprietary hardware firewalls or concentrators for gateways. Cloud-native software-defined perimeters (SDP) offer infinitely more flexibility, geographic scalability, and easier maintenance without hardware depreciation.
5. Understanding Budget Tiers
Entry-Level ($3 - $6 per user/month): These are typically small business VPNs offering centralized billing, basic team seat management, and shared global servers. They are excellent for encrypting traffic on public Wi-Fi and securing basic browsing but are limited in granular, application-level access controls.
Mid-Range ($7 - $12 per user/month): The optimal sweet spot for most modern businesses. Solutions in this tier offer robust ZTNA architectures, cloud firewalls (FWaaS), dedicated gateway IP options, and comprehensive SSO integrations.
Enterprise (Custom Pricing): Top-tier SASE platforms featuring advanced threat prevention, continuous identity risk assessment, integrated Data Loss Prevention (DLP), and 24/7 dedicated account management. Pricing here is highly negotiated and dependent on seat volume and specific security module requirements.
FAQ
What is the difference between a traditional VPN and Zero Trust Network Access (ZTNA)?
A traditional VPN connects a remote user to the entire corporate network, meaning if an attacker breaches the VPN, they can potentially access everything. ZTNA connects a user only to specific, authorized applications and continuously verifies their identity and device health, significantly reducing the attack surface.
Which protocol is best for a business VPN in 2026?
WireGuard is currently the industry standard for business VPNs. It offers significantly faster connection speeds, lower latency, and uses state-of-the-art cryptography. Proprietary protocols like Lightway (ExpressVPN) or NordLynx (NordLayer) are also excellent, as they are often built on WireGuard's foundation.
Do I need a dedicated IP address for my remote team?
Yes, if you use cloud services (like AWS, Salesforce, or internal databases) that require IP whitelisting for security. A dedicated IP ensures that your team always appears to be connecting from the same trusted location, preventing access blocks.
What is split tunneling and why is it important?
Split tunneling allows administrators to route specific corporate traffic through the encrypted VPN tunnel while letting standard internet traffic (like streaming Spotify or browsing YouTube) travel on the user's regular local network. This preserves corporate bandwidth and improves overall connection speed.
How does SSO integrate with a business VPN?
Single Sign-On (SSO) allows employees to log into their VPN using their existing corporate credentials (via Okta, Google Workspace, Azure AD, etc.). It simplifies the login process, allows IT to enforce Multi-Factor Authentication (MFA), and makes onboarding/offboarding employees instant.
What does 'device posture check' mean?
Device posture checks are a ZTNA feature that verifies the health of an endpoint before granting access. The system checks if the device has an updated OS, active antivirus, and an encrypted hard drive. If the device fails the check, access to corporate resources is denied.
Are consumer VPNs safe for business use?
Consumer VPNs are safe for basic privacy on public Wi-Fi, but they are not suitable for securing corporate infrastructure. They lack centralized admin controls, user provisioning, ZTNA policies, and dedicated IPs, making them unmanageable for IT departments.
How did you measure speed in the M2 Evaluation framework?
We measured Connection Speed & Latency by simulating high-bandwidth file transfers and continuous VoIP calls across various global server locations, calculating upload/download retention percentages and latency ping overhead during both idle and peak congestion periods.
Which VPN is best for a small startup?
Tailscale is highly recommended for startups due to its zero-configuration setup, excellent WireGuard speeds, and ability to create secure peer-to-peer mesh networks without requiring dedicated IT security staff.
What is microsegmentation?
Microsegmentation is a security technique that divides a network into isolated segments down to the individual workload or application level. If a breach occurs in one segment, the attacker cannot move laterally into other segments.
Do enterprise VPNs offer Service Level Agreements (SLAs)?
Yes, top-tier enterprise SASE and ZTNA providers like Cloudflare, Zscaler, and Check Point offer strict SLAs guaranteeing 99.99% or higher network uptime, accompanied by 24/7 dedicated support channels.
Can a business VPN block malware and phishing sites?
Yes, many modern business VPNs and SASE platforms include DNS filtering and Cloud Firewalls (FWaaS) that automatically block known malicious domains, phishing sites, and command-and-control servers at the network edge before they reach the user.
What is a hardware-free software-defined perimeter?
It is a security architecture that uses lightweight software connectors deployed in the cloud or on-premise, brokering secure access to applications without requiring the purchase, installation, or maintenance of physical firewall appliances.
Methodology
Our Methodology
To accurately rank the top business VPNs and ZTNA platforms of 2026, we employed the M2 Multi-Dimensional Evaluation model, a strictly evidence-based scoring framework designed to eliminate editorial bias, brand favoritism, and subjective preference. Our evaluation methodology isolates specific software performance vectors, ensuring each product is judged entirely on measurable technical metrics that directly correlate to real-world corporate IT operational needs.
Scoring Framework and Core Dimensions
Every candidate in our extensive pool of 35 VPN solutions was systematically and rigorously scored from 1 to 10 across seven heavily researched dimensions. These dimensions, and their respective impact weight on the overall score, were established through extensive consultation with certified network engineers, CISOs, and IT administrators:
- Security & Encryption Protocols (20%): We meticulously analyzed encryption cipher standards (AES-256, ChaCha20), protocol availability (WireGuard, Lightway, proprietary Stealth protocols), implementation of strict no-logs policies, and the presence of independent compliance certifications (SOC 2 Type II, ISO 27001).
- Admin Management & Deployment (20%): We measured the exact friction of deployment, evaluating the intuitiveness of centralized control panels, automated user provisioning (SCIM), and the depth of native integrations with major identity providers like Okta, Azure AD, and Google Workspace.
- Zero Trust & Advanced Features (15%): We assessed the architectural maturity of Zero Trust Network Access (ZTNA), software-defined perimeters (SDP), microsegmentation capabilities, granular split tunneling, DNS filtering, and continuous endpoint device posture checks.
- Connection Speed & Latency (15%): Utilizing a battery of automated synthetic tests, we recorded upload/download speed retention percentages and latency ping overhead during both idle and peak network congestion periods to objectively gauge performance impact on remote end-users.
- Global Server Network Infrastructure (10%): We mathematically mapped the geographic distribution of each provider's edge network, counting total global Points of Presence (PoPs), the availability of dedicated corporate IP gateways, and overall cloud infrastructure uptime reliability.
- End-User App Experience (10%): We evaluated client software design and stability across Windows, macOS, Linux, iOS, and Android ecosystems. High scores were awarded for intuitive UI design, quick-connect reliability, background stability, and minimal battery/RAM drain.
- Pricing & Scalability (10%): We calculated the true total cost of ownership (TCO) by analyzing transparent per-user monthly costs, minimum seat requirements, tiered feature restrictions, and the flexibility of billing structures for rapidly scaling teams.
Scenario-Based Algorithmic Rankings
Because a fast-moving, 20-person startup's operational needs differ wildly from a heavily regulated multinational enterprise, we utilized algorithmic weighting to generate scenario-specific rankings. By mathematically adjusting the dimensional weights according to the use-case, we identified the best overall solutions for balanced workforces, the top picks for high-security enterprise environments prioritizing Zero Trust architecture over cost, the best budget-friendly and zero-config options for startups, and the leading platforms for global speed and heavy bandwidth requirements.
Sources & References
All factual claims, product specifications, prices, and images in this article are cited by number. Click any reference to jump to the list; click the link in each entry to visit the original source.
- [1]SelectionLogic. "M2 Multi-Dimensional Evaluation." selectionlogic.org/en/methods/m2-multi-dimensional-evaluation/. Accessed Mar 2026.
- [2]SelectionLogic. "Business VPN Buying Guide 2026." selectionlogic.org/en/guides/business-vpn-buying-guide/. Accessed Mar 2026.
- [3]Cloudflare. "Cloudflare Zero Trust." cloudflare.com/products/zero-trust/. Accessed Mar 2026.
- [4]Tailscale. "Tailscale Mesh VPN." tailscale.com. Accessed Mar 2026.
- [5]Zscaler. "Zscaler Private Access." zscaler.com/products/zscaler-private-access. Accessed Mar 2026.
- [6]Twingate. "Twingate Zero Trust." twingate.com. Accessed Mar 2026.
- [7]Nord Security. "NordLayer." nordlayer.com. Accessed Mar 2026.
- [8]Check Point. "Perimeter 81." perimeter81.com. Accessed Mar 2026.
- [9]Cisco. "Cisco Secure Client." cisco.com/c/en/us/products/security/secure-client/index.html. Accessed Mar 2026.
- [10]ExpressVPN. "ExpressVPN Official Site." expressvpn.com. Accessed Mar 2026.
- [11]Windscribe. "Windscribe ScribeForce." windscribe.com/scribeforce. Accessed Mar 2026.
- [12]Tom's Guide. "The ultimate guide to VPNs: everything you need to know." tomsguide.com. Accessed Mar 2026.
- [13]Security.org. "What Is a VPN? A Complete Guide to Virtual Private Networks." security.org. Accessed Mar 2026.
- [14]Surfshark. "Surfshark for Teams." surfshark.com/teams. Accessed Mar 2026.
- [15]Proton AG. "Proton VPN for Business." protonvpn.com/business. Accessed Mar 2026.
- [16]Palo Alto Networks. "GlobalProtect." paloaltonetworks.com. Accessed Mar 2026.
- [17]Fortinet. "FortiClient." fortinet.com. Accessed Mar 2026.
- [18]Netskope. "Netskope Private Access." netskope.com. Accessed Mar 2026.
- [19]Appgate. "Appgate SDP." appgate.com. Accessed Mar 2026.
- [20]Jamf. "Jamf Connect." jamf.com. Accessed Mar 2026.
- [21]Absolute Software. "NetMotion Mobility." absolute.com. Accessed Mar 2026.
- [22]Banyan Security. "Banyan Security ZTNA." banyansecurity.io. Accessed Mar 2026.
- [23]GoodAccess. "GoodAccess Cloud VPN." goodaccess.com. Accessed Mar 2026.
- [24]UTunnel. "UTunnel VPN." utunnel.io. Accessed Mar 2026.
- [25]Ivanti. "Ivanti Connect Secure." ivanti.com. Accessed Mar 2026.